Identity Proofing vs Authentication: What's The Difference?


When a patient launches a third-party app that pulls data from their EHR, two distinct security processes are at work, and conflating them creates real risk. Identity proofing vs authentication may sound like a semantic debate, but the difference between the two determines whether you're verifying who someone is for the first time or confirming they're the same person who showed up before. In healthcare, getting this wrong isn't just an inconvenience, it's a compliance liability.
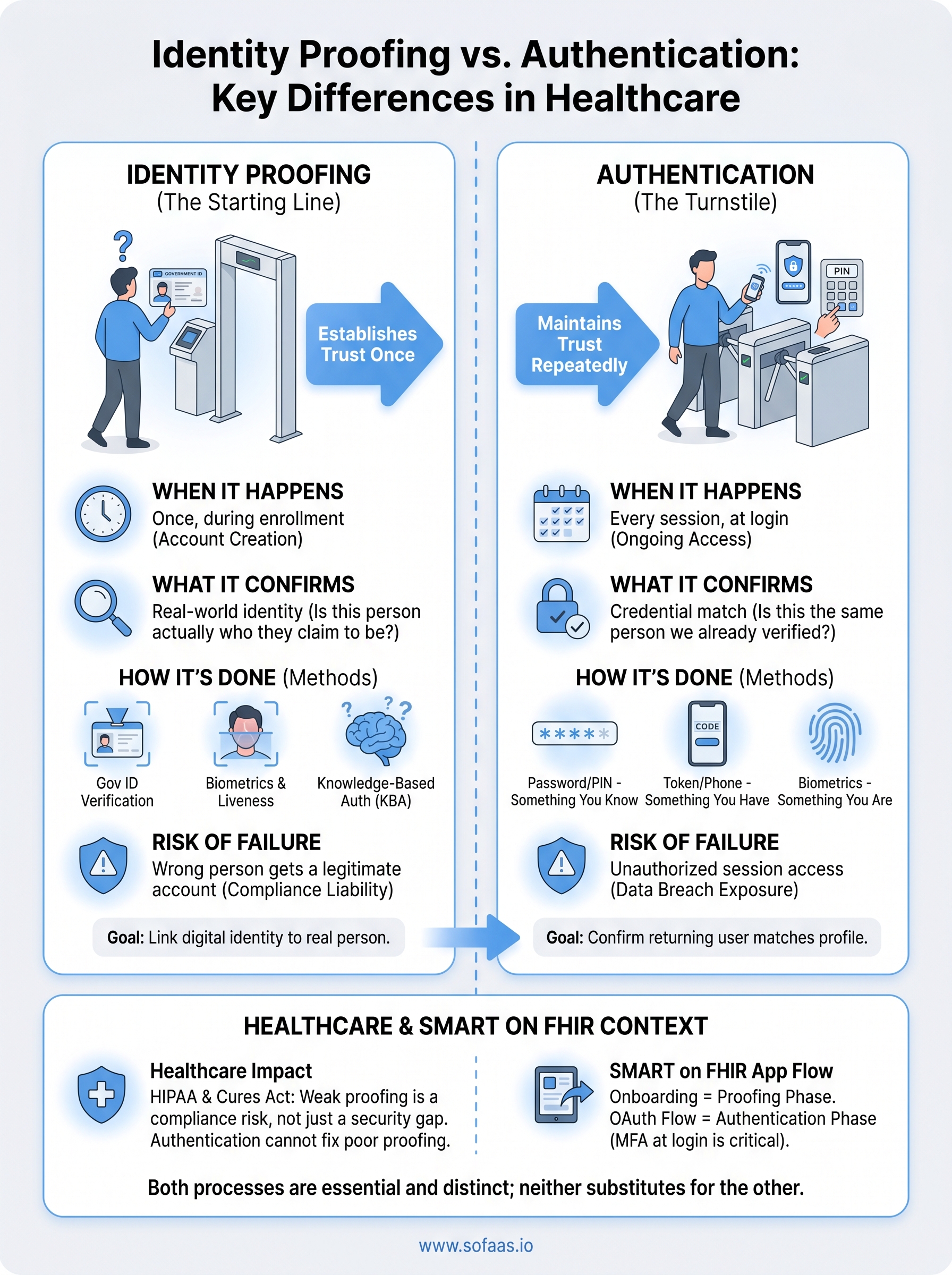
Identity proofing establishes trust at the starting line. Authentication maintains it every time after. Both are essential to secure healthcare workflows, but they operate at different stages of the user lifecycle and rely on fundamentally different methods. If your application connects to EHRs and handles patient data, understanding where each process fits isn't optional.
This distinction matters especially in contexts like SMART on FHIR integrations, where OAuth flows manage patient authorization and access control across systems. At SoFaaS, we build and manage that authorization layer, handling token management, consent flows, and secure EHR connectivity, so healthcare application teams can focus on their product instead of infrastructure. But regardless of how your integration is architected, your team needs a solid grasp of both identity proofing and authentication to build something patients and providers can trust.
This article breaks down what each process does, how they differ, where they overlap, and why both matter in healthcare application development.
What identity proofing and authentication mean
Both terms describe security checkpoints, but they answer different questions at different points in a user's lifecycle. Identity proofing asks: "Is this person actually who they claim to be?" Authentication asks: "Is this the same person we already verified?" One happens once, at enrollment. The other happens repeatedly, every time a user wants access to a system.
What identity proofing does
Identity proofing is the process of establishing a user's real-world identity before they gain access to a system for the first time. You typically encounter this step during account creation or onboarding. The goal is to link a digital identity to a verifiable, real-world person by collecting and validating credentials that only that specific individual should possess.
Common identity proofing methods include:
- Government-issued ID verification: scanning a passport or driver's license
- Knowledge-based authentication (KBA): questions drawn from credit or public records
- Biometric verification: matching a live selfie against a photo ID
- In-person proofing: face-to-face verification with a credentialed agent
Identity proofing is not a one-time formality. In regulated industries, it determines whether your system can legally treat a digital identity as trustworthy before granting access to sensitive data.
The level of rigor your proofing process requires depends on what the user will access and the risk associated with that access. The NIST Digital Identity Guidelines (SP 800-63) define three Identity Assurance Levels (IALs) that describe how thoroughly you need to verify a user based on the sensitivity of the data involved. If your application handles protected health information, IAL2 or IAL3 is the applicable standard, requiring either remote or in-person verification with validated identity evidence.
What authentication does
Authentication is the process of confirming that a returning user is the same person who was previously proofed and credentialed. You deal with this every time a user logs in. Rather than re-establishing identity from scratch, authentication checks whether the credentials being presented match a stored, trusted profile.
Recognizing the identity proofing vs authentication distinction matters here because authentication only works as well as the proofing that preceded it. If someone slipped through a weak proofing process, even a rigorous authentication system will continue granting them access to data they should not see. The two processes are sequential and directly dependent on each other.
Authentication methods fall into three categories:
- Something you know: password or PIN
- Something you have: hardware token or one-time code sent to a registered device
- Something you are: fingerprint or facial recognition
Modern systems combine at least two of these into multi-factor authentication (MFA), which significantly reduces the risk of unauthorized access even when a single factor is compromised or stolen.
Why the difference matters in healthcare
Healthcare sits at the intersection of sensitive personal data and strict regulatory requirements, which makes the identity proofing vs authentication distinction more consequential here than in most other industries. When a patient or provider accesses health records through a connected application, every step in that access chain carries legal weight. A failure at the proofing stage doesn't just create a security gap, it creates a compliance exposure that regulators can act on.
HIPAA and the cost of weak proofing
HIPAA's Security Rule requires covered entities and their business associates to implement reasonable safeguards for protected health information (PHI). If your application onboards a user with weak identity proofing, you may be granting access to PHI to someone whose identity you never actually confirmed. Authentication controls alone cannot compensate for that gap because authentication only verifies that the credentials presented match what's on file, not that the underlying identity is legitimate.
A system with strong authentication but weak identity proofing is effectively a high-security lock on a door with no frame.
Breach notifications, HHS investigations, and reputational damage are all potential outcomes of getting this wrong. Your compliance posture depends on both processes working correctly, not just one of them, and auditors will scrutinize each separately.
How patient access requirements raise the stakes
The 21st Century Cures Act and related ONC rules expanded patients' rights to access their own health data through third-party applications. This means more apps, more access points, and more opportunities for identity failures at onboarding. When you build an application under these rules, you are responsible for ensuring that the person requesting data access is actually the patient that data belongs to, not just a user who holds valid login credentials. That responsibility begins at proofing, not at login.
The key differences at a glance
The simplest way to separate identity proofing vs authentication is by asking when each process runs and what it confirms. Proofing happens once, at onboarding, binding a digital account to a real, verifiable person. Authentication happens at every login, confirming that whoever holds the credentials matches the account already on file. Both are necessary, but neither substitutes for the other.

| Identity Proofing | Authentication | |
|---|---|---|
| When it runs | Once, during enrollment | Every session, at login |
| What it confirms | Real-world identity | Credential match |
| Primary evidence | Government ID, biometrics, KBA | Password, token, biometric |
| Failure consequence | Wrong person gets a legitimate account | Unauthorized session access |
How scope and timing separate them
Your identity proofing process runs at the boundary between the public internet and your system. It is a gate that only opens once per user. Authentication is the turnstile that operates on every subsequent visit. Scope matters here: proofing is broad and investigative, pulling in external data sources to validate a claim. Authentication is narrow and transactional, comparing a presented credential against a stored record.
The key distinction by timeline:
- Proofing: runs once, at onboarding, before the account exists
- Authentication: runs every session, after the account is established
What each one protects against
Identity proofing protects against account takeover at the source, stopping a bad actor from establishing a fraudulent identity in your system from day one. Authentication protects against session hijacking and credential theft for accounts that already exist. The threats are different, which is why both controls need to be sized correctly to the risk.
- Proofing failure risk: a synthetic or stolen identity gains a real, persistent account
- Authentication failure risk: a valid account gets accessed in an unauthorized session
Treating authentication as a substitute for rigorous identity proofing is one of the most common and costly mistakes in healthcare application security.
Common methods and threat coverage
Understanding identity proofing vs authentication at a conceptual level only gets you so far. What matters in practice is knowing which specific methods belong to each process and which threats each one is designed to block. Picking the right combination depends on what data your application handles and the risk profile of your user base.
Identity proofing methods and what they stop
Your proofing process needs to connect a digital account to a verified, real-world person before that account can exist. The methods you use determine how much trust you can place in the identities your system accepts.

Common identity proofing methods include:
- Document verification: scanning a government-issued ID and checking it against authoritative databases
- Biometric liveness detection: matching a selfie to a photo ID and confirming the user is physically present, not a photo or video replay
- Knowledge-based authentication (KBA): questions drawn from credit bureaus or public records that only the real person should be able to answer
- In-person proofing: face-to-face verification with a trained agent for the highest-assurance scenarios
These methods specifically block synthetic identity fraud, where someone constructs a plausible-but-fake person using real data fragments, and account creation fraud, where a bad actor tries to register using someone else's stolen identity.
Authentication methods and what they stop
Once a user has a verified account, your authentication controls determine whether every subsequent login is legitimate. The threat here shifts from fake identity creation to unauthorized access against real accounts.
Authentication methods map to three factor types:
- Something you know: passwords and PINs, the weakest factor when used alone
- Something you have: hardware tokens, authenticator apps, or one-time codes sent to a registered device
- Something you are: fingerprint scans or facial recognition tied to enrolled biometrics
Multi-factor authentication (MFA) combines at least two of these factors, reducing the impact of credential theft, phishing, and session hijacking, which are the primary risks authentication is built to address.
How to apply this to SMART on FHIR apps
When you build a SMART on FHIR application, the identity proofing vs authentication split maps directly onto two distinct phases of your integration. Your onboarding flow is where proofing happens, and your OAuth authorization flow is where authentication operates. Understanding which phase owns which responsibility helps you design a system that satisfies both HIPAA requirements and ONC data access rules without over-engineering either layer.
Identity proofing in your SMART on FHIR onboarding
Before a patient or provider can authorize your app to access EHR data, you need to confirm who you are actually enrolling. This is where identity proofing sits in your workflow. If you're building a patient-facing app, you must verify that the person creating an account matches the patient record they're requesting access to. Weak proofing at this stage means your OAuth flow will happily hand real PHI to the wrong person, and no amount of strong authentication will fix that downstream.
Your SMART on FHIR app inherits trust from your proofing process. If that trust is weak at enrollment, every authorized session after it carries the same flaw.
Authentication within the OAuth flow
Once a patient or provider has a verified account, your SMART on FHIR OAuth flow manages the authentication side. The SMART on FHIR specification uses OAuth 2.0 to handle token issuance and scoped access, but it does not define how you authenticate the user before the authorization step begins. That responsibility belongs to your application layer. You need to enforce MFA at login and tie your token request to a confirmed, active session, not just a stored credential. Managing this correctly means your app grants access only when the right verified person is actively present, not just when someone holds a valid token.
Quick wrap-up and next step
The core takeaway from the identity proofing vs authentication discussion is straightforward: both processes are necessary and neither substitutes for the other. Identity proofing confirms who someone is before their account exists. Authentication confirms that the same verified person is present at every subsequent login. In healthcare applications, weakening or skipping either process creates a compliance exposure that regulators, patients, and auditors will all scrutinize independently.
Your SMART on FHIR application inherits trust from both layers. If you want to get the authorization and token management layer right without building it from scratch, the infrastructure work does not have to slow your team down. SoFaaS manages consent flows, secure EHR connectivity, and OAuth token handling across major EHR systems so you can stay focused on your product. Launch your SMART on FHIR app and connect to Epic, Cerner, and Allscripts in days, not months.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.