Google BeyondCorp Zero Trust: How It Works Without VPNs Today


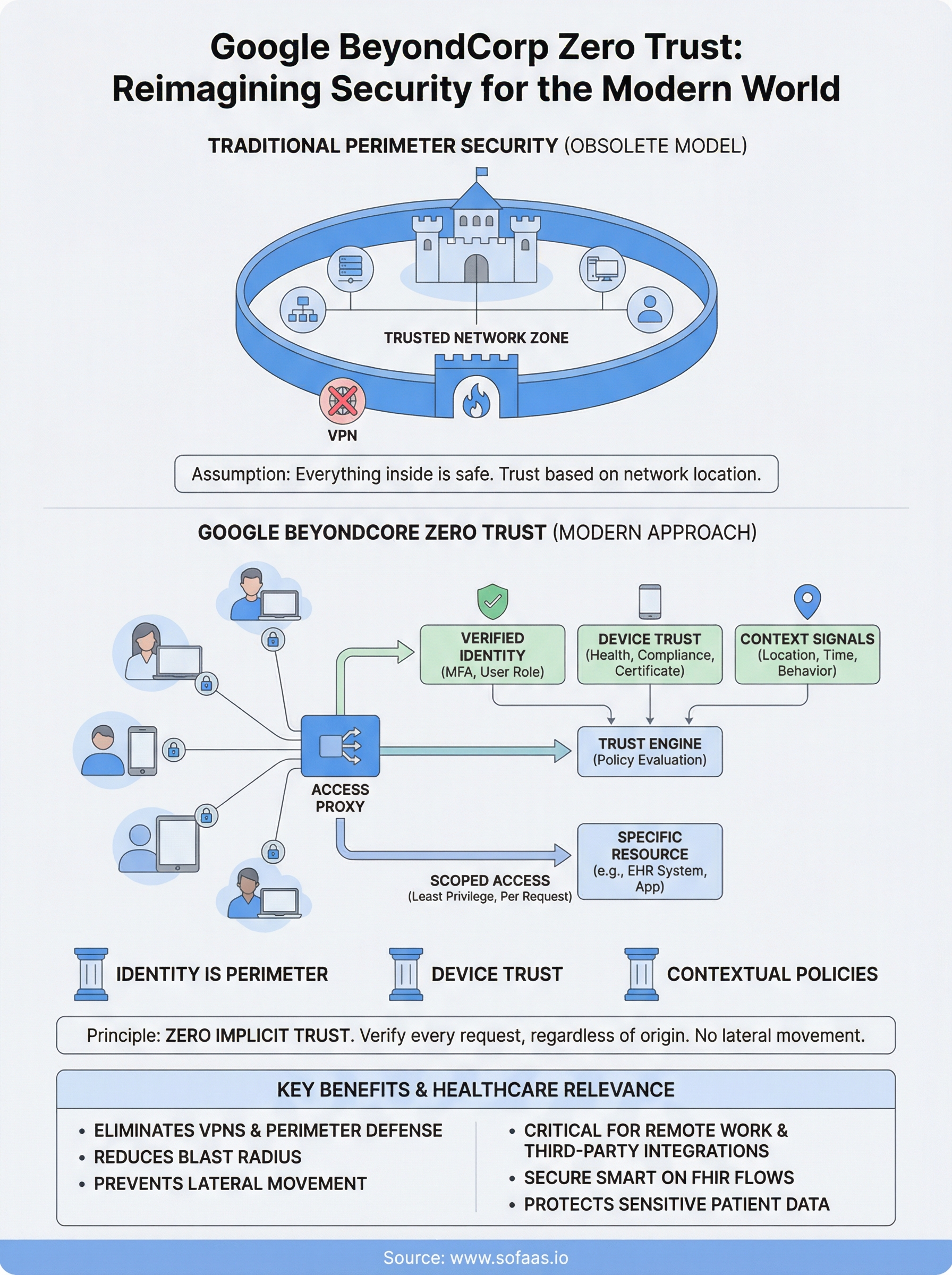
Traditional network security assumed that everything inside the corporate perimeter was trustworthy. Google's BeyondCorp zero trust model threw that assumption out entirely. Instead of relying on VPNs and firewalls to create a "safe zone," BeyondCorp shifts access decisions to the individual user and device level, every request is verified, regardless of where it originates.
For teams building healthcare applications, this isn't just an interesting security philosophy. It's directly relevant. At SoFaaS, we manage SMART on FHIR integrations between third-party apps and EHR systems, and every connection depends on identity-based authorization, not network location. The principles behind BeyondCorp mirror what modern healthcare integration demands: granular access control, continuous verification, and zero implicit trust between systems handling sensitive patient data.
This article breaks down how Google's BeyondCorp framework actually works, what its core architectural components are, and why it eliminates the need for traditional VPNs. Whether you're a CTO evaluating security models or a developer building on healthcare infrastructure, understanding this framework gives you a sharper lens on how identity-driven security operates at scale.
Why BeyondCorp matters in modern zero trust programs
For decades, enterprise security was built on a single assumption: keep attackers out, and trust everything inside. That worked when employees worked from fixed offices and applications ran on on-premise servers. But cloud adoption, distributed workforces, and the surge in third-party integrations dismantled that model. The perimeter dissolved, and security teams were left defending a boundary that no longer existed in any practical sense.
When the perimeter disappears, trust based on network location becomes a liability, not an asset.
Google's BeyondCorp framework emerged directly from that problem. Beginning in 2014, Google published a series of research papers documenting how it moved its entire workforce off a privileged corporate network, replacing implicit internal trust with continuous, context-aware access decisions tied to verified user identity and device health. No VPN, no safe zone, no assumed trust for any internal request.
How the modern threat landscape made perimeter security obsolete
Remote work, cloud infrastructure, and mobile devices eliminated any meaningful distinction between "inside" and "outside" the network. When your users connect from home offices, shared workspaces, and personal devices, the idea of a trusted internal network is a fiction. A compromised device sitting behind the corporate firewall is just as dangerous as an external attacker, and traditional security tools cannot tell the difference.
Lateral movement, where an attacker gains initial access and then moves freely through a flat internal network, is one of the most consistently documented patterns in enterprise breaches. Perimeter-based models concentrate all protective value at the edge and leave almost nothing to stop an attacker who gets through. The blast radius is enormous because internal systems extend implicit trust to anything that made it past the firewall.
Why google beyondcorp zero trust changes the calculation
The google beyondcorp zero trust approach eliminates the concept of implicit internal trust entirely. Access decisions happen per request, based on verified identity, real-time device compliance checks, and contextual signals. If a device fails a health check or a credential is compromised, access is denied or scoped down immediately, regardless of where the request originates or what network it's coming from.
For industries handling sensitive data, including healthcare, this distinction carries real operational weight. Patient records, clinical workflows, and authorization flows are high-value targets. A perimeter-based model means one successful breach potentially exposes all of it. A zero trust model built on BeyondCorp principles contains the damage at the request level, so a stolen credential or compromised endpoint doesn't automatically translate into unrestricted data access.
Your architecture decisions today reflect how well you understand this shift. Whether you're managing EHR integrations, handling patient authorization flows, or building any system where identity verification and access control are non-negotiable, the principles behind BeyondCorp give you a concrete blueprint for what secure access looks like without depending on network location as a trust signal.
BeyondCorp principles and core components
Google's BeyondCorp framework rests on a set of principles that replace network location with verified identity and device state as the foundation for every access decision. Understanding these principles matters because they define the architecture you'd need to replicate this model, whether you're running internal tooling or building systems that handle sensitive external data like patient records and EHR connections.
Identity as the new perimeter
User identity sits at the center of every BeyondCorp access decision. The framework relies on a centralized identity provider that authenticates users through strong credentials, typically enforced through multi-factor authentication and tied to a single authoritative directory. Access policies check who you are before anything else, and that check happens on every request, not just at initial login.
Identity replaces the network edge as the primary control point in the BeyondCorp model.
Your access policies map specific user identities to specific resources, with permissions scoped tightly to what each role actually requires. This eliminates the wide-open internal access that perimeter models grant by default to anyone who clears the outer firewall.
Device trust and context signals
Device trust is the second critical component. Every device attempting to access a resource must meet a defined compliance baseline, verified in real time through an inventory database that tracks device health, OS version, patch status, and certificate validity. A device that falls out of compliance loses access immediately, regardless of the user's credentials.
Beyond identity and device state, BeyondCorp incorporates contextual signals like geographic location, request timing, and behavioral patterns to score each access attempt. The google beyondcorp zero trust model routes all of these signals through a policy enforcement point that sits between users and resources, evaluating every request against current policy rather than assumed historical trust. No request inherits access from a previous session, which directly cuts off the lateral movement opportunities that flat internal networks create.
How BeyondCorp access works without a VPN
Traditional VPNs create an encrypted tunnel that drops you onto a trusted internal network. Once you're in, you typically get broad access to whatever that network segment permits. BeyondCorp removes that tunnel entirely, replacing it with a different architecture that never grants network-level access in the first place. Every resource sits behind an access proxy, and every request must pass evaluation before it reaches anything.
The access proxy as the enforcement point
The access proxy is the central mechanism that makes VPN-free access possible. When you request access to an internal application, your request hits the proxy first, not the application itself. The proxy calls out to a trust engine that evaluates your identity, device compliance state, and contextual signals in real time. If the evaluation passes, the proxy forwards the request to the specific resource you asked for, nothing else. You never touch the underlying network.

The access proxy enforces least-privilege at the request level, so a single verified session grants access to one resource, not an entire network segment.
How user and device credentials work together
Your user credentials alone aren't enough to gain access under this model. The system also checks whether your device holds a valid certificate issued by the organization, and whether that device currently meets the compliance baseline stored in the device inventory. Both signals must satisfy the active policy. If your device failed a recent patch check or your certificate expired, the request gets denied, even when your username and password are correct.
This combination of user identity plus device-level verification is what fundamentally separates the google beyondcorp zero trust model from a VPN. A VPN validates a single credential at the tunnel entry point. BeyondCorp validates multiple independent signals on every request, scoped precisely to the resource being accessed, with no persistent network access granted at any point during the session.
BeyondCorp vs VPNs and perimeter security models
VPNs and perimeter security models share a core assumption: the network boundary is what separates trusted from untrusted. You authenticate once at the edge, and everything behind it extends broad network-level access based on that single credential check. That model was designed for a fixed infrastructure that no longer reflects how most organizations actually operate, especially in healthcare where third-party app connections and remote access are daily operational realities.
What VPNs actually protect
A VPN establishes an encrypted tunnel between your device and the corporate network, but what it protects is the channel, not the resource. Once the tunnel is up, the network treats your device as trusted. Your access extends as far as the network segment permits, which in flat architectures can mean a wide range of systems. If your device is compromised before or during that session, the VPN does nothing to limit the damage.
Perimeter-based firewalls follow the same logic. They inspect traffic entering from outside and block what doesn't match approved rules, but they have no mechanism to evaluate real-time device health or the identity context of every individual request once traffic is inside. The outer wall is defended, and everything behind it moves freely.
Where BeyondCorp wins the comparison
The google beyondcorp zero trust model never grants network access at all. You get access to a specific resource, verified per request, based on your identity and device state at that exact moment. There is no lateral movement opportunity because there is no internal network to traverse. Each resource is its own access decision, evaluated independently.
BeyondCorp reduces the blast radius of a compromised credential from "everything on the network" to "one specific resource, temporarily."
For any system managing sensitive data, this comparison is decisive. VPNs protect the transport channel. BeyondCorp protects each resource directly with continuous verification that adjusts in real time. If your threat model includes credential theft or compromised endpoints, the perimeter model gives you one line of defense. BeyondCorp gives you one per request.
How to implement BeyondCorp style zero trust
Implementing a BeyondCorp-style architecture doesn't require you to replicate Google's exact internal infrastructure, but it does require you to rethink access from the ground up. Your starting point is accepting that network location carries no trust value, and rebuilding every access control around identity and device state instead.
Consolidate identity and device inventory
Your first concrete step is establishing a single authoritative identity provider that covers every user accessing your systems. Enforce multi-factor authentication across all accounts and eliminate any access path that bypasses that provider entirely.
At the same time, build a device inventory database that tracks every endpoint, including its OS version, patch status, and certificate validity. Without this inventory, you have no reliable signal to evaluate device health against your access policies, and every access decision you make rests on incomplete data.
A device inventory is not optional in the BeyondCorp model: it is the foundation every access decision depends on.
Deploy an access proxy and write resource-specific policies
Once your identity and device signals are in place, put an access proxy in front of every application or resource you want to protect. Nothing should be directly reachable without passing through that proxy first. Google's own BeyondCorp Enterprise platform offers a managed path to this architecture if you're building on Google Cloud, and it handles the proxy and policy engine components in a single managed service.
After your proxy is in place, write explicit access policies for each individual resource, scoped to the minimum identity and device requirements that each role actually needs. The google beyondcorp zero trust model gains its precision from tight, resource-specific policies that limit what any single verified session can reach. Review these policies on a defined schedule, because device compliance baselines and user roles shift over time, and stale policies silently reintroduce the same implicit trust problems you built this architecture to eliminate.
Key takeaways and next steps
The google beyondcorp zero trust model replaces one outdated assumption with a stronger foundation: network location proves nothing. Every access decision depends on verified identity and real-time device compliance, evaluated per request, with no implicit trust extended to anything or anyone. That shift changes your entire threat model from defending a perimeter to protecting each individual resource.
Your practical path forward starts with consolidating identity, building a device inventory, and placing access proxies in front of every sensitive resource you control. These three steps apply whether you're securing internal tooling or managing healthcare data integrations that connect third-party applications to EHR systems.
If your work involves connecting healthcare apps to EHR systems, that access layer is where these principles become non-negotiable. Launch your SMART on FHIR integration and see how a managed platform handles identity-based authorization and compliance without the infrastructure overhead you'd otherwise build from scratch.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.