What Is Identity Proofing? Definition, Steps, And Examples


What Is Identity Proofing? Definition, Steps, And Examples
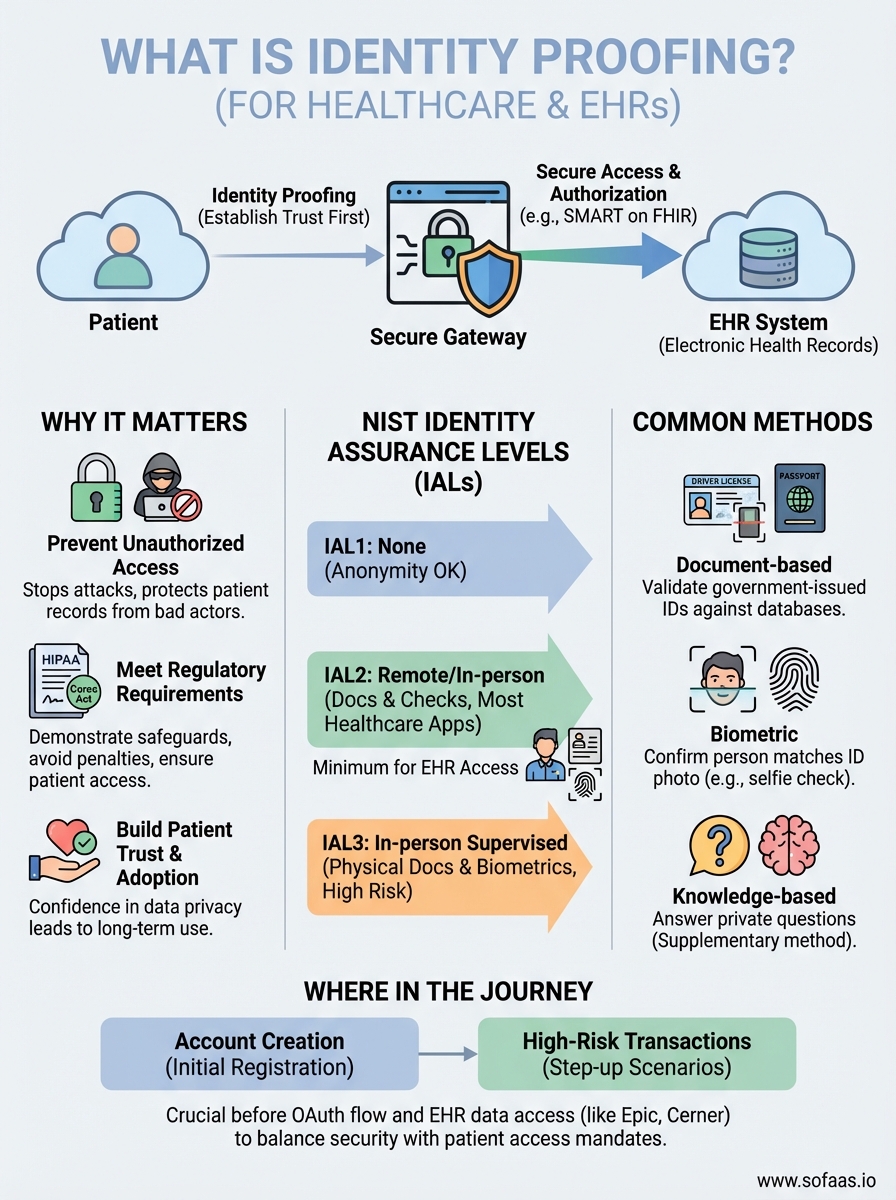
When a patient tries to access their health records through your application, how do you know they are who they claim to be? Understanding what is identity proofing is essential for any healthcare technology team building applications that connect to Electronic Health Records. It's the foundational process that establishes trust before any sensitive medical data changes hands.
For companies developing SMART on FHIR applications, the kind that SoFaaS helps connect to EHRs like Epic and Cerner, identity proofing sits at the heart of secure patient authorization. It's not just a compliance checkbox for HIPAA; it's how you protect patients and maintain the integrity of every data exchange. Without it, your OAuth flows and consent management processes are built on uncertain ground.
This article breaks down the complete definition of identity proofing, walks through each step of the process, and provides real-world examples you can reference. You'll also learn how identity proofing differs from identity verification and authentication, terms that often get confused but serve distinct purposes in your security architecture.
Why identity proofing matters for security and trust
You cannot build secure healthcare applications without establishing who your users actually are before they access patient data. Identity proofing creates the baseline for every security decision that follows in your application. When you skip this step or implement it poorly, you open the door to unauthorized access that can expose thousands of patient records in a single breach.
Preventing unauthorized access to sensitive health data
Healthcare applications face constant threats from bad actors attempting to access patient medical records through stolen credentials or synthetic identities. Identity proofing stops these attacks at the gate by requiring proof that the person requesting access actually exists and matches the identity they claim. Your application verifies documents, checks government databases, and confirms biometric markers before granting access to any health information.
The consequences of weak identity proofing hit healthcare organizations hard. Data breaches in 2025 cost healthcare providers an average of $10.93 million per incident, according to IBM's annual security report. Most of these breaches started with compromised credentials that passed through authentication systems because no proper identity proofing occurred during account creation.
Without strong identity proofing, you're simply trusting that users are who they say they are, which is exactly what attackers count on.
Meeting regulatory requirements and compliance standards
HIPAA requires that you implement reasonable safeguards to ensure only authorized individuals access protected health information. Identity proofing serves as your first line of defense in meeting this requirement. Your organization must demonstrate that you verified user identities before granting access to EHR systems, and weak proofing methods won't satisfy auditors when they review your security controls.
Beyond HIPAA, the 21st Century Cures Act mandates that patients have electronic access to their health information without unnecessary barriers. This creates a tension you must balance: making access convenient while ensuring only legitimate patients get through. Strong identity proofing resolves this tension by streamlining verification for real patients while blocking fraudulent attempts.
Building patient confidence and long-term adoption
Patients need to trust that their most sensitive personal information stays protected when they use your healthcare application. You build this trust by implementing identity proofing that patients can see and experience. When your application asks for document verification or biometric confirmation, you signal that security matters and that you're protecting their data from unauthorized viewers.
Trust directly impacts your application's success metrics. Healthcare apps with strong identity proofing see higher long-term adoption rates because patients feel confident their records remain private. Conversely, applications that suffer breaches due to weak identity controls lose users permanently. Your reputation in healthcare hinges on security, and understanding what is identity proofing means understanding how to protect both patients and your business.
How identity proofing works under NIST guidelines
The National Institute of Standards and Technology provides the definitive framework for identity proofing through its Digital Identity Guidelines (NIST SP 800-63A). These guidelines establish three distinct Identity Assurance Levels that determine how rigorously you verify someone's identity based on the sensitivity of the data or systems they want to access. Understanding what is identity proofing means knowing these levels guide every verification decision you make for your healthcare application.
The three identity assurance levels explained
NIST structures identity proofing into three progressive levels that increase in verification rigor. Identity Assurance Level 1 (IAL1) requires no identity proofing at all because the application doesn't need to know who the user actually is. You use this level for services where anonymity is acceptable and no personal data gets accessed.

Identity Assurance Level 2 (IAL2) requires remote or in-person proofing using government-issued identity documents and additional verification checks. You verify that the evidence is genuine, validate it against authoritative sources, and confirm the person presenting the evidence is its rightful owner. Healthcare applications connecting to EHRs typically require IAL2 at minimum because you're dealing with protected health information.
Identity Assurance Level 3 (IAL3) demands in-person proofing at a supervised location where trained staff examine physical identity documents and capture biometric data. You reserve this level for the highest-risk scenarios, though most healthcare applications find IAL2 sufficient for patient authorization workflows.
The level you choose directly impacts both your security posture and your users' onboarding experience, so you must balance protection with accessibility.
Evidence collection and validation requirements
NIST requires you to collect specific identity evidence types during proofing, categorized as strong, superior, fair, or weak. Strong evidence includes unexpired government-issued photo IDs like driver's licenses or passports. You must verify this evidence through multiple methods: checking security features, validating against issuing authority databases, and confirming the person matches the document through biometric comparison or knowledge-based verification questions.
Your system needs to detect and reject fraudulent documents using automated tools that check for tampering, forgery, or stolen identity credentials. For IAL2, you combine document verification with additional checks like phone number validation or address confirmation against authoritative public records.
Common identity proofing methods and examples
You implement identity proofing through several distinct verification methods, each offering different levels of security and user friction. Healthcare applications typically combine multiple methods to achieve the identity assurance level required by NIST guidelines and HIPAA regulations. Understanding what is identity proofing in practice means knowing which methods work best for your specific patient authorization workflows and how to layer them for maximum protection.
Document-based verification methods
Your application collects and validates government-issued identity documents like driver's licenses, passports, or state ID cards during the proofing process. You capture images of these documents through mobile camera uploads or desktop scanners, then your system analyzes them for security features like holograms, microprinting, and UV-reactive elements that indicate authenticity. Automated verification services compare the document data against issuing authority databases to confirm it hasn't been reported stolen or forged.
A patient opening a new account might photograph their driver's license using their smartphone camera. Your system extracts the name, date of birth, and address, then cross-references this information with motor vehicle department records to validate the license is active and matches the captured image. This method works particularly well for remote identity proofing where patients never visit a physical location.
Biometric authentication techniques
Biometric verification confirms the person presenting the identity document actually owns that identity by comparing physical characteristics. You capture a selfie or live video of the user and use facial recognition algorithms to match it against the photo on their government ID. This prevents someone from using a stolen or borrowed document to impersonate another person.
Advanced biometric methods include fingerprint scanning, iris recognition, or voice analysis. Healthcare applications requiring IAL3 assurance often combine facial recognition with document verification in a supervised enrollment session where trained staff witness the entire proofing process.
Knowledge-based verification approaches
Your system asks verification questions that only the legitimate identity holder should know based on public records and credit history. These questions reference past addresses, previous loan amounts, or associated phone numbers that bad actors cannot easily research. You present multiple-choice questions and require the user to answer most or all correctly within a time limit to pass proofing.
Knowledge-based verification works best as a supplementary method rather than your sole proofing technique, since data breaches have compromised many personal details.
A patient might answer questions about their mortgage lender or the street they lived on five years ago. This method adds minimal friction while strengthening your overall identity assurance when combined with document verification.
Where to use identity proofing in the user journey
You place identity proofing at specific touchpoints where you need to establish or re-establish trust before granting access to protected resources. Knowing what is identity proofing helps you determine exactly where verification should occur in your application flow. The timing of these verification steps directly impacts both your security posture and your conversion rates, since you must balance protection with user experience.

Account creation and initial registration
Your strongest opportunity for identity proofing occurs during account creation when users expect additional verification steps. You should implement proofing immediately after basic registration information gets collected but before any access to health records happens. This moment gives you the cleanest path to verify identity documents, capture biometric data, and validate information against authoritative sources without disrupting an active workflow.
Healthcare applications typically require users to complete identity proofing before they can authorize access to their EHR data through SMART on FHIR workflows. You collect government-issued IDs, verify the person matches the document, and establish the baseline identity that all future authentication checks will reference. Completing this verification early means users face no delays when they actually need to access their medical records.
Your initial proofing creates the foundation for every security decision your application makes throughout the entire user relationship.
High-risk transactions and step-up scenarios
You implement additional identity proofing when users attempt actions that carry elevated risk beyond routine data access. Changing primary contact information, adding new authorized users, or requesting bulk data exports should trigger step-up verification that confirms the current user still owns the account. This prevents account takeover attacks where bad actors gain initial access through stolen credentials but cannot complete high-value actions without passing fresh proofing checks.
Your system might require users to re-verify their identity through document uploads or biometric scans when they request access to particularly sensitive records like mental health notes or substance abuse treatment history. These step-up moments let you apply proportional security based on the sensitivity of the specific transaction.
Identity proofing for healthcare apps and EHR access
Healthcare applications face unique identity proofing challenges because you must verify patients before granting access to their Electronic Health Records while maintaining compliance with both security regulations and patient access mandates. Understanding what is identity proofing in healthcare contexts means recognizing that you're not just protecting data but also enabling patient rights to view and manage their own medical information. Your proofing implementation directly affects whether patients can exercise these rights without unnecessary barriers.
SMART on FHIR authorization requirements
Your SMART on FHIR applications require identity proofing before patients can authorize access to their EHR data through OAuth workflows. You must verify the patient's identity matches the medical record they're requesting access to, preventing unauthorized individuals from viewing another patient's health information. This verification typically happens during the initial account setup when patients first connect your application to their provider's EHR system.
The OAuth authorization flow itself does not perform identity proofing since it only handles authentication and consent management after identity gets established. You implement proofing as a prerequisite step that validates the person creating the account actually owns the medical records associated with that identity. Healthcare providers like Epic and Cerner require this verification before they allow third-party applications to access patient data through their FHIR APIs.
Your identity proofing implementation determines whether your SMART on FHIR integration meets provider security requirements and gains approval for production use.
Balancing security with patient access mandates
You face regulatory pressure from multiple directions when implementing identity proofing for healthcare applications. HIPAA demands strong verification to prevent unauthorized access, while the 21st Century Cures Act prohibits information blocking and requires you to provide patients reasonable access to their electronic health information. Your proofing process must be rigorous enough to satisfy security requirements yet streamlined enough that legitimate patients don't face excessive friction.
Modern healthcare applications solve this tension by implementing risk-based proofing that adjusts verification requirements based on the sensitivity of requested data and the context of access. You might accept lower assurance levels for viewing basic demographic information while requiring stronger proofing for accessing mental health records or requesting bulk data exports.
Next steps
You now understand what is identity proofing means for your healthcare application and how it protects patient data throughout your EHR integration workflows. Your next move is choosing which identity assurance level matches your application's risk profile and implementing verification methods that meet NIST guidelines while keeping patient onboarding smooth.
Start by auditing your current user registration flow to identify where identity proofing gaps exist. Healthcare applications connecting to EHRs through SMART on FHIR need robust proofing mechanisms before patients authorize data access, so you must address these gaps before launching production integrations with provider systems.
Document verification vendors and biometric authentication services offer ready-made solutions that integrate into your existing application architecture. Select providers who specialize in healthcare compliance and understand the specific requirements of patient identity verification under HIPAA regulations.
If you're building a healthcare application that needs to connect to Epic, Cerner, or other major EHR systems, VectorCare's SoFaaS platform handles the complexity of SMART on FHIR integration while you focus on implementing the identity proofing that protects your patients and meets compliance requirements.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.