Role-Based Access Control vs Attribute-Based Access Control


Role-Based Access Control vs Attribute-Based Access Control
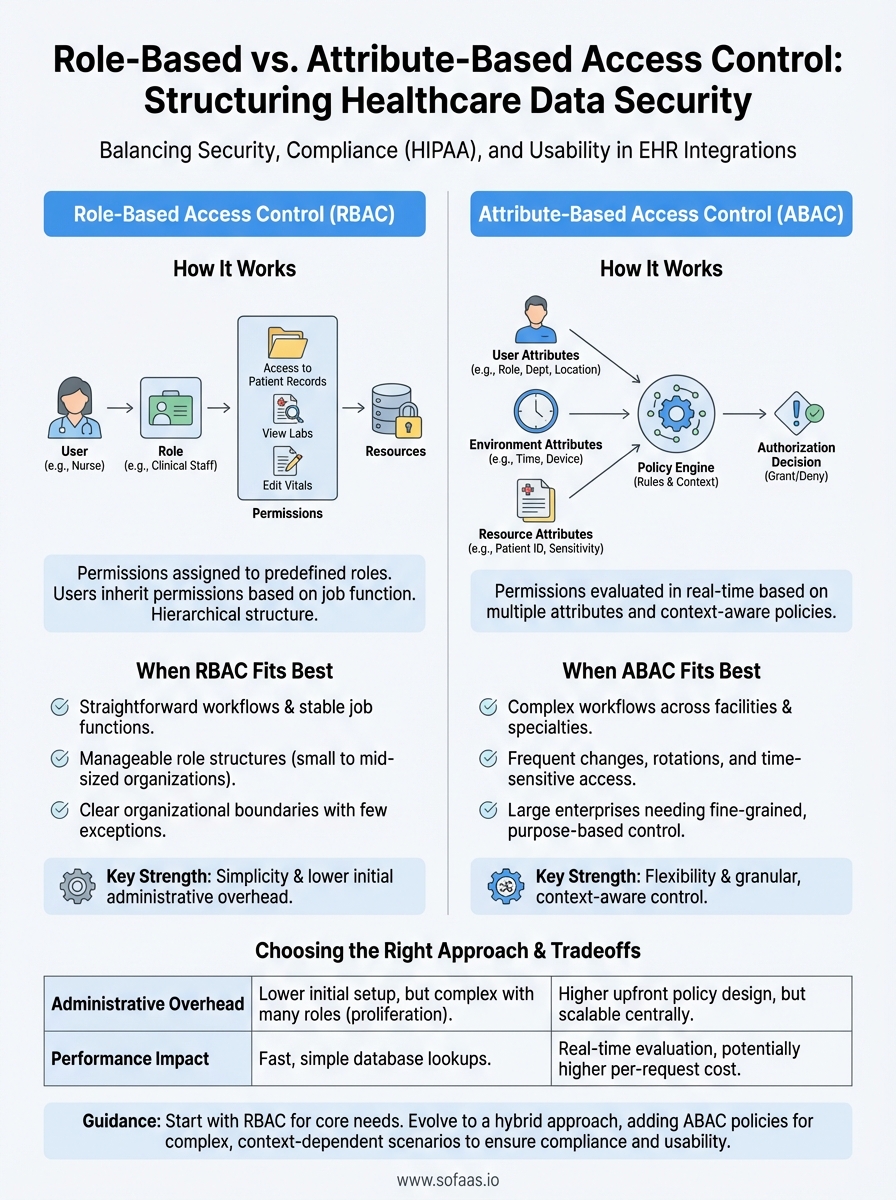
When building healthcare applications that connect to EHRs, controlling who can access patient data isn't just a security checkbox, it's a compliance requirement and an ethical obligation. The choice between role-based access control vs attribute-based access control shapes how your application handles permissions, scales with complexity, and meets regulatory demands like HIPAA.
At SoFaaS, we help healthcare innovators integrate with EHRs through SMART on FHIR, and authorization decisions are central to every implementation we support. Whether you're building a patient portal, a clinical decision support tool, or a supplier management system, understanding these two access models helps you design permissions that work for your users and your compliance team alike.
This article breaks down the technical differences between RBAC and ABAC, examines their strengths and limitations, and provides guidance on choosing the right approach, or combining both, for your healthcare application.
Why access control models matter for modern apps
You can't afford to treat access control as an afterthought when patient data flows through your application. Every authorization decision your system makes creates either a layer of protection or a potential vulnerability. The difference between role based access control vs attribute based access control isn't academic, it determines whether your permissions scale with your user base or collapse under their complexity.
Security breaches cost more than engineering time
Healthcare data breaches averaged $10.93 million per incident in 2023, according to IBM's Cost of a Data Breach Report, making healthcare the most expensive industry for security failures. Your access control model directly influences this risk. When a breach occurs because permissions were too broad or poorly managed, you don't just face financial penalties, you lose customer trust and face potential lawsuits from affected patients.
Poor access control design creates hidden vulnerabilities that audits rarely catch until after an incident. If a nurse can access records for patients they never treated, or if a billing clerk can view clinical notes they don't need, your application has excessive privilege exposure. These over-permissioned accounts become targets for attackers and create liability during investigations.
The cost of implementing granular access control upfront is always lower than the cost of explaining why you didn't after a breach.
Compliance frameworks demand audit trails
HIPAA's minimum necessary rule requires that you limit access to the smallest amount of protected health information needed for a specific purpose. This isn't a suggestion, it's a regulatory requirement that influences how you design permissions. Your access control model must support detailed logging of who accessed what data, when, and why.
Auditors look for evidence that your system enforces separation of duties and prevents unauthorized access. If your model can't produce clear reports showing that only appropriate users accessed specific patient records, you fail compliance checks. Traditional role-based systems struggle with this when roles become too broad, while attribute-based systems can provide the fine-grained logging regulators expect.
User expectations have shifted permanently
Your users expect context-aware permissions that adapt to their current needs without creating friction. A physician covering the emergency department overnight needs different access than during their regular clinic hours. DME suppliers need temporary access to verify patient orders without permanent database privileges.
Static permission assignments frustrate users and encourage workarounds that undermine security. When clinicians can't access the data they need quickly, they share credentials, write down passwords, or request overly broad access to avoid future blocks. Your access control model must balance security with usability, providing the right access at the right time without creating administrative overhead that scales poorly.
Application teams that ignore these dynamics build systems that either lock out legitimate users or grant excessive privileges to everyone. Neither outcome serves your security posture or your user experience.
How RBAC works and when it fits best
Role-based access control assigns permissions to predefined roles rather than individual users, then maps users to those roles based on their job functions. When you add a new nurse to your application, you assign them the "Nurse" role, and they instantly inherit all permissions associated with that role. This approach mirrors organizational structure, making it intuitive for administrators who think in terms of job titles and departments rather than granular permission sets.
Core mechanics of role assignment
Your RBAC system maintains three key relationships: users belong to roles, roles contain permissions, and permissions grant access to resources. When a user requests access to a patient record, the system checks which roles that user holds, then evaluates whether any of those roles include the necessary permission. This hierarchical structure simplifies management because you modify the role once, and the change propagates to all users assigned to that role.

Most RBAC implementations support role hierarchies where senior roles inherit permissions from junior roles. A Chief Physician role automatically includes all permissions granted to the Physician role, plus additional administrative capabilities. This inheritance prevents duplication and ensures consistency across your permission structure.
RBAC works best when your organization has stable job functions with clear boundaries and limited exceptions.
Best use cases for RBAC
Healthcare applications with straightforward workflows benefit most from RBAC. If your DME supplier portal serves three distinct user types (ordering physicians, fulfillment staff, billing team) with minimal overlap in their needs, RBAC provides exactly what you need. The model excels when job functions predict access requirements accurately, and when most users within a role need identical permissions.
Small to mid-sized organizations see the greatest advantage because their role structures remain manageable. When you have 5-10 well-defined roles serving a few hundred users, RBAC delivers security without complexity. The administrative overhead stays low, audit logs remain readable, and onboarding new users takes minutes instead of hours. Understanding role based access control vs attribute based access control helps you recognize that RBAC's simplicity becomes its limitation only when your permission requirements outgrow fixed role definitions.
How ABAC works and when it fits best
Attribute-based access control evaluates multiple attributes about the user, the resource, the environment, and the action to make authorization decisions dynamically. Instead of checking whether you belong to a pre-assigned role, ABAC examines characteristics like your department, the patient's assigned care team, the time of day, the data sensitivity level, and the purpose of access. This model creates context-aware permissions that adapt to circumstances rather than relying on static role assignments.
Attribute evaluation in real time
Your ABAC system combines attributes into policy rules that express complex conditions. A policy might state that physicians can view lab results only for patients on their active care team, only during their scheduled shift, and only from devices on the hospital network. Each access request triggers evaluation of these conditions against current attribute values, which means permissions change automatically when circumstances change without administrator intervention.

ABAC policies use Boolean logic to create sophisticated rules: "Grant access if (user.department = Cardiology AND patient.location = Cardiology-Floor-3 AND time.hour BETWEEN 06:00 AND 18:00)." This flexibility lets you encode your organization's actual security requirements instead of approximating them with broad role definitions.
ABAC shines when your access decisions depend on context that changes frequently or when exceptions outnumber your standard cases.
When ABAC solves what RBAC cannot
Healthcare organizations with complex workflows across multiple facilities, specialties, and care teams need ABAC's flexibility. If your application serves a hospital network where physicians rotate through departments, where patients move between units, and where temporary staff need time-limited access, ABAC handles these dynamics without creating hundreds of micro-roles. The comparison of role based access control vs attribute based access control reveals that ABAC handles scenarios where permissions must respond to real-time conditions rather than static assignments.
Large enterprises with thousands of users benefit most because ABAC scales with attribute combinations rather than role proliferation. When your permission requirements include too many special cases for RBAC to manage cleanly, ABAC provides the granularity you need while maintaining centralized policy control. Regulatory requirements demanding purpose-based access also push organizations toward ABAC, since the model naturally supports restrictions based on why someone needs data, not just who they are.
RBAC vs ABAC tradeoffs that decide the winner
The choice between role based access control vs attribute based access control comes down to practical tradeoffs that affect your development timeline, operational costs, and long-term maintenance burden. Neither model wins universally because each excels in different scenarios, and your application's specific requirements determine which tradeoffs you can accept. Understanding these differences helps you avoid building a system that works initially but becomes unsustainable as complexity grows.
Administrative overhead and policy management
RBAC demands less initial setup because you define a finite set of roles that map to organizational structure. Your team creates 10-15 roles in a few days, assigns users, and moves forward. Changes require updating role definitions or creating new roles, which takes minutes when your permission needs remain stable. This simplicity breaks down when you need 50+ roles to handle exceptions, at which point role management becomes more complex than the problems you tried to solve.
ABAC requires upfront policy design that takes weeks instead of days because you must identify all relevant attributes, define their relationships, and build policy rules that encode your security requirements. Once implemented, though, policy changes happen centrally without touching individual user assignments. When your physician rotation schedule changes, ABAC policies adapt automatically because they reference current schedule attributes rather than static role memberships.
Administrative burden shifts from ongoing role proliferation in RBAC to initial policy complexity in ABAC.
Performance impact and technical debt
RBAC evaluates permissions through simple database lookups that check role membership and return quickly. Your application queries whether a user belongs to a role that has permission for an action, and the database index handles this efficiently even with thousands of users. This speed comes at the cost of flexibility and accuracy when your actual security requirements include contextual factors that roles cannot express.
ABAC performs real-time attribute evaluation that queries multiple data sources to gather current context before making authorization decisions. Each access request might check the user's department, the patient's care team roster, the current time, and the device location. This computation costs more per request but delivers granular accuracy that prevents excessive privilege exposure.
How to choose and implement RBAC, ABAC, or both
Your implementation decision starts with honest assessment of your current permission requirements and your capacity to manage complexity. Most healthcare applications benefit from starting simple and adding sophistication only when clear needs emerge. The right choice between role based access control vs attribute based access control depends on whether your security requirements fit neatly into job functions or demand context-aware decisions that adapt to changing circumstances.
Assess your organization's permission patterns
You need to evaluate whether your access decisions cluster around job titles or depend on dynamic factors. Look at your existing users and document when they need different permissions than their peers in the same role. If 80% of your users fit cleanly into 5-10 roles with rare exceptions, RBAC solves your problem without unnecessary complexity. Your analysis should identify whether exceptions represent temporary situations that will normalize or permanent requirements that signal the need for ABAC.
Count how often you create new roles to handle special cases. When your role list grows beyond 20 and continues expanding, you have reached the point where role proliferation costs more than ABAC policy management. Organizations with stable workflows and clear organizational boundaries get maximum value from RBAC's simplicity, while those with frequent rotations, cross-functional teams, and time-sensitive access requirements need ABAC's flexibility.
Implementation complexity should match your actual security requirements, not your theoretical ideal of perfect granularity.
Start with RBAC and evolve toward ABAC
Your safest path begins with basic RBAC that covers your primary use cases, then adds ABAC selectively for scenarios where roles fail. This hybrid approach lets you deliver working permissions quickly while building the infrastructure to handle complex cases. You implement core roles for physicians, nurses, and administrative staff using RBAC, then layer ABAC policies for time-limited access, emergency overrides, or location-based restrictions.
Technical implementation requires policy decision points that evaluate both role memberships and attribute conditions. Your authorization service checks RBAC rules first for speed, then evaluates ABAC policies for requests that need contextual decisions.
Next steps
Your authorization strategy affects every integration decision you make when building healthcare applications. The debate between role based access control vs attribute based access control resolves when you match your permission complexity to your actual security requirements rather than implementing sophistication for its own sake. Most teams succeed by starting with RBAC for core workflows and adding ABAC policies only where context determines access rights.
Building secure EHR integrations requires more than choosing the right access control model. You need compliant infrastructure, pre-built connectors, and authorization flows that work across multiple EHR systems without rebuilding your security layer for each vendor. Launch your Smart on FHIR app with VectorCare's managed platform that handles OAuth flows, patient consent, and HIPAA-compliant data access so you can focus on building features instead of wrestling with integration complexity. Your access control decisions become simpler when your integration layer already handles the authorization mechanics correctly.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.