mTLS vs TLS: Key Differences, Handshake, And Best Use Cases


mTLS vs TLS: Key Differences, Handshake, And Best Use Cases
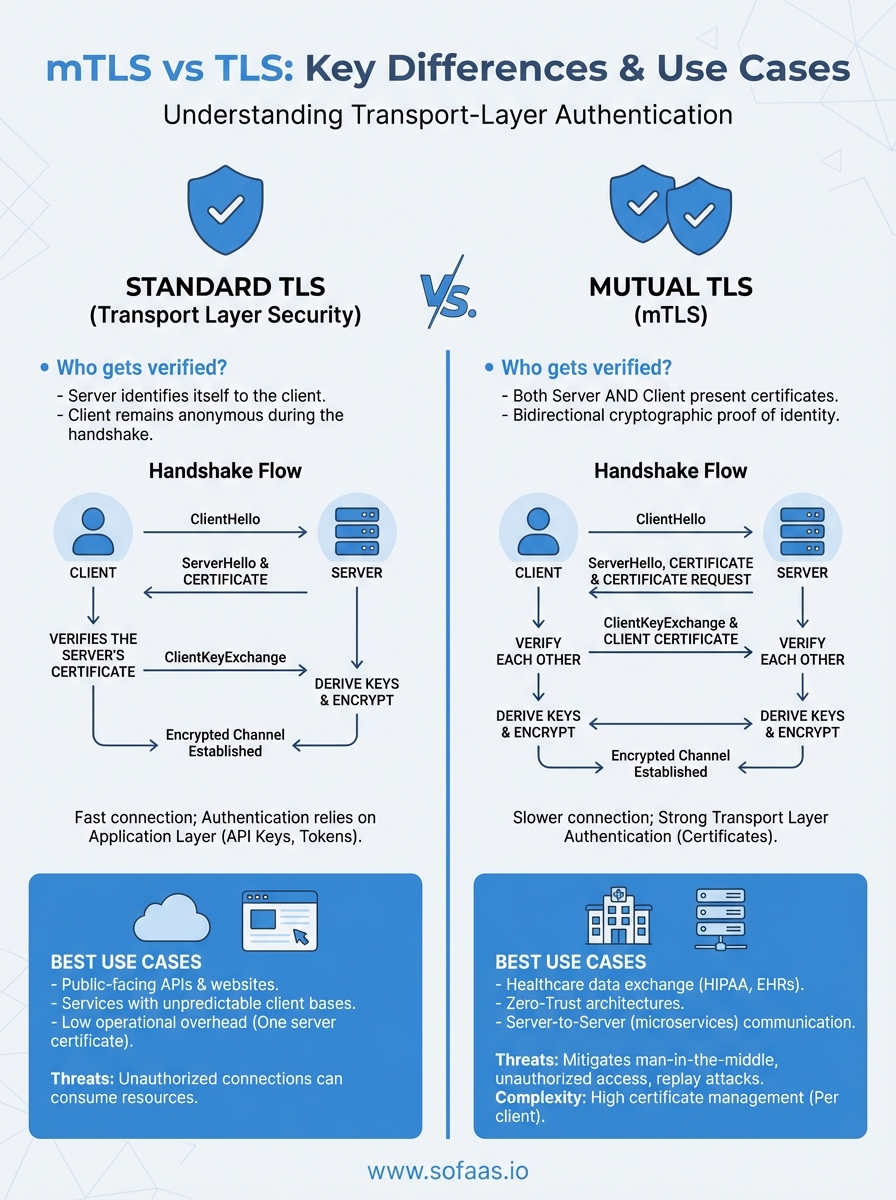
Securing healthcare data in transit requires more than just encryption, it demands authentication that proves both parties are who they claim to be. When comparing mTLS vs TLS, the distinction comes down to one critical factor: who gets verified during the connection handshake.
Standard TLS authenticates the server to the client, confirming you're connecting to the right endpoint. Mutual TLS (mTLS) takes this further by requiring both sides to present certificates, creating a two-way trust model. For healthcare applications integrating with EHRs through platforms like SoFaaS, understanding when to use each protocol directly impacts your security architecture and compliance posture, especially when handling sensitive patient data under HIPAA requirements.
This article breaks down the technical differences between TLS and mTLS, walks through how each handshake process works, and identifies the scenarios where mutual authentication becomes essential. By the end, you'll know exactly which protocol fits your use case and why that choice matters for your healthcare integration strategy.
Why the difference matters in real systems
The choice between mTLS vs TLS directly affects your security posture, operational complexity, and regulatory compliance. Standard TLS works well when you trust clients to identify themselves through application-layer credentials like API keys or OAuth tokens. This model scales easily because you don't need to provision and manage certificates for every connecting client. Your server verifies its own identity, and clients authenticate after the encrypted tunnel exists.
Mutual TLS changes this equation by moving authentication into the transport layer itself. Before any application data flows, both parties prove their identity through cryptographic certificates. This shift matters most when you cannot rely on application-layer security alone or when regulatory frameworks demand cryptographic proof of identity before data transmission begins.
When standard TLS falls short
Application-layer authentication introduces a timing vulnerability that matters in high-security environments. With standard TLS, your server establishes an encrypted connection before knowing who the client is. An attacker can connect, consume server resources, and potentially probe for vulnerabilities before you reject them at the application layer. Healthcare systems handling protected health information cannot afford this attack surface.
In healthcare integrations, the moment you accept a connection, you create liability under HIPAA. If that connection comes from an unauthorized party, even for milliseconds, you've potentially exposed your system to a reportable incident.
Certificate management complexity
Standard TLS requires you to manage one certificate per server. Your IT team renews these certificates annually, updates DNS records, and coordinates with certificate authorities. The operational overhead remains predictable and manageable. Most teams handle this with automated tools like Let's Encrypt or enterprise certificate management systems.

Mutual TLS multiplies this complexity by the number of clients you serve. Every connecting application needs its own certificate, a revocation strategy when compromised, and a distribution mechanism that maintains security. If you're building a SaaS platform connecting 50 healthcare providers, you now manage 50 client certificates plus your server certificates. Each certificate needs monitoring, rotation schedules, and emergency revocation procedures.
Compliance alignment in healthcare
HIPAA's Security Rule requires you to implement authentication mechanisms that uniquely identify users and systems. While username and password combinations technically satisfy this requirement, auditors increasingly expect cryptographic authentication for system-to-system communications. When your application exchanges patient demographics or clinical data with an EHR, demonstrating mutual authentication through certificates provides clear evidence of compliance.
Regulatory frameworks like HITRUST and SOC 2 Type II explicitly call out mutual authentication as a control objective for sensitive data exchanges. If your healthcare application connects to multiple EHR systems through an integration platform, the authentication model you choose determines which controls you can claim during audits. Standard TLS with API keys might pass technical scrutiny but fails to demonstrate the same level of trust that mTLS certificates provide.
How TLS authentication and encryption work
Standard TLS creates a one-way authentication model where only the server proves its identity to connecting clients. When you visit a website or your application connects to an API endpoint, the server presents a digital certificate signed by a trusted Certificate Authority. Your client verifies this certificate against its list of trusted authorities, confirms the certificate hasn't expired or been revoked, and then proceeds with establishing an encrypted connection. This process protects you from man-in-the-middle attacks where an attacker intercepts traffic by impersonating the legitimate server.
Server identity verification
The server's certificate contains its public key and identifying information like domain name, organization, and validity period. Your client checks that the domain in the certificate matches the domain you intended to reach. Certificate Authorities like DigiCert, Let's Encrypt, or Sectigo act as trusted third parties that vouch for the server's identity by signing these certificates with their own private keys. When your client trusts the CA, it automatically trusts any certificate that CA has signed.
The certificate chain creates a trust hierarchy where your client only needs to trust a handful of root CAs to verify millions of servers across the internet.
The encryption handshake
After verifying the server's identity, your client and the server negotiate which encryption algorithms they both support. They agree on a cipher suite that determines how data gets encrypted, authenticated, and verified for integrity. Your client generates a session key using the server's public key from its certificate, and only the server can decrypt this session key with its corresponding private key. Both parties now share symmetric encryption keys that secure all subsequent data transmission. This symmetric encryption runs faster than public key cryptography, which is why TLS uses it for bulk data transfer after the initial handshake completes. Understanding standard TLS helps clarify the mtls vs tls distinction when we examine how mutual authentication changes this process.
How mTLS adds client authentication
Mutual TLS extends the standard TLS handshake by requiring clients to present their own digital certificates before the server accepts the connection. When you implement mTLS, your server no longer trusts any client that can establish an encrypted tunnel. Instead, it demands cryptographic proof of identity that works exactly like server authentication in reverse. Your client must possess a valid certificate signed by a Certificate Authority that your server recognizes, and this verification happens during the transport layer handshake before any application data flows.
Client certificate requirements
Your client needs a private key and public certificate pair that your server can validate. This certificate contains identifying information about the client application or system, such as organization name, common name, and validity period. When you deploy mTLS, you must decide whether to use publicly trusted CAs or private certificate authorities that you control internally. Most healthcare integrations choose private CAs because they provide complete control over certificate issuance and revocation without relying on external parties or paying per-certificate fees.
The certificate itself becomes the authentication credential, eliminating the need to transmit passwords or API keys that could be intercepted or logged.
Bidirectional trust establishment
The fundamental difference in the mtls vs tls comparison centers on who proves their identity and when. Standard TLS creates a one-way trust where clients verify servers but remain anonymous until application-layer authentication occurs. Mutual TLS requires both parties to verify certificates before establishing the encrypted tunnel. Your server validates the client's certificate using the same cryptographic checks that clients perform on server certificates. This bidirectional verification means unauthorized parties cannot even complete the handshake, protecting your server from connection attempts by unknown or compromised clients before they consume resources or probe for vulnerabilities.
How the TLS and mTLS handshakes differ
The handshake sequence reveals where the mtls vs tls protocols diverge in their authentication approach. Both protocols follow similar initial steps, exchanging cipher suite negotiations and establishing encryption parameters. The critical difference emerges when the server requests authentication from the client. Standard TLS skips this step entirely, while mTLS adds an extra round trip where the client must present and prove ownership of its certificate. This additional verification step adds latency to connection establishment but provides cryptographic identity confirmation before any application data flows.

Standard TLS handshake flow
Your client initiates contact by sending a ClientHello message that lists supported cipher suites and TLS versions. The server responds with a ServerHello, selecting the strongest mutually supported options, then immediately sends its certificate and public key. Your client verifies this certificate against its trusted CA store, generates a pre-master secret encrypted with the server's public key, and sends it back. Both sides derive session keys from this secret, send encrypted confirmation messages, and the handshake completes. At this point, your client remains anonymous to the server. Any authentication happens later through application-layer credentials like API keys or OAuth tokens transmitted over the now-encrypted channel.
Standard TLS completes in fewer round trips because only one party must prove their identity during the initial handshake.
Mutual TLS handshake additions
Mutual TLS inserts a certificate request step after the server sends its own certificate. Your server specifies which Certificate Authorities it trusts, and your client must respond with a matching certificate plus a digitally signed message that proves it possesses the corresponding private key. The server validates this client certificate using the same verification process clients use for server certificates. This bidirectional verification means both parties confirm each other's identity before deriving session keys. The additional round trip typically adds 50-100 milliseconds to connection establishment, but eliminates the need for separate authentication mechanisms at the application layer.
Best use cases and trade-offs for each approach
The decision between standard TLS and mTLS depends on your threat model and operational capacity to manage certificates at scale. Standard TLS provides strong encryption and server authentication with minimal operational overhead, making it suitable when you control authentication through application-layer mechanisms. Mutual TLS delivers transport-layer authentication that eliminates entire classes of attacks but requires certificate lifecycle management for every client system you connect with. Your choice impacts not just security but also deployment complexity and ongoing maintenance costs.
When standard TLS fits your needs
Standard TLS works well for public-facing APIs where you cannot predict or control who connects to your service. If you run a SaaS platform serving thousands of customers through web browsers or mobile apps, provisioning individual certificates for each user becomes impractical. Your application handles authentication after the encrypted connection exists using OAuth tokens, API keys, or session cookies. This approach scales efficiently because you only manage server certificates while clients authenticate through credentials your application validates.
Most REST APIs, webhook receivers, and customer-facing services operate successfully with standard TLS. You gain encryption in transit, server identity verification, and compatibility with virtually any client that supports HTTPS. The tradeoff accepts that unauthorized parties can initiate connections and consume resources until your application rejects them based on credentials.
When mTLS becomes essential
Mutual TLS solves problems that standard TLS cannot address when you need cryptographic proof of client identity before processing any data. Healthcare integrations exchanging patient information between known systems require this bidirectional trust. When your application connects to EHR systems through platforms like SoFaaS, mTLS ensures both endpoints verify each other before protected health information flows across the network. Zero-trust architectures mandate mutual authentication between all services regardless of network location.
The mtls vs tls decision becomes clear when regulatory frameworks explicitly require cryptographic authentication or when you implement microservices that must verify each service's identity.
Server-to-server communications in high-security environments justify the operational complexity of managing client certificates. You accept longer initial handshakes and certificate distribution challenges in exchange for eliminating credential theft, replay attacks, and unauthorized access attempts at the transport layer.
Key takeaways
The mtls vs tls decision hinges on whether you need transport-layer authentication for both parties or server-side verification alone. Standard TLS provides encryption and server authentication with minimal operational overhead, making it ideal for public-facing services where you manage client identity through application credentials. Mutual TLS adds bidirectional certificate verification that eliminates unauthorized connection attempts before they consume resources or access your systems.
Healthcare applications exchanging patient data between known systems require the cryptographic trust model that mTLS delivers. You gain compliance alignment with HIPAA and HITRUST requirements while protecting sensitive information at the transport layer. The tradeoff involves managing client certificates across all connecting systems, but this complexity becomes manageable when you automate certificate provisioning and rotation through the right integration platform.
If you're building healthcare applications that connect to EHR systems, you need secure authentication built into your infrastructure from day one. Launch your Smart on FHIR app with enterprise-grade security and compliance already configured.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.