Business Associate Agreement Definition: HIPAA BAA Overview


Business Associate Agreement Definition: HIPAA BAA Overview
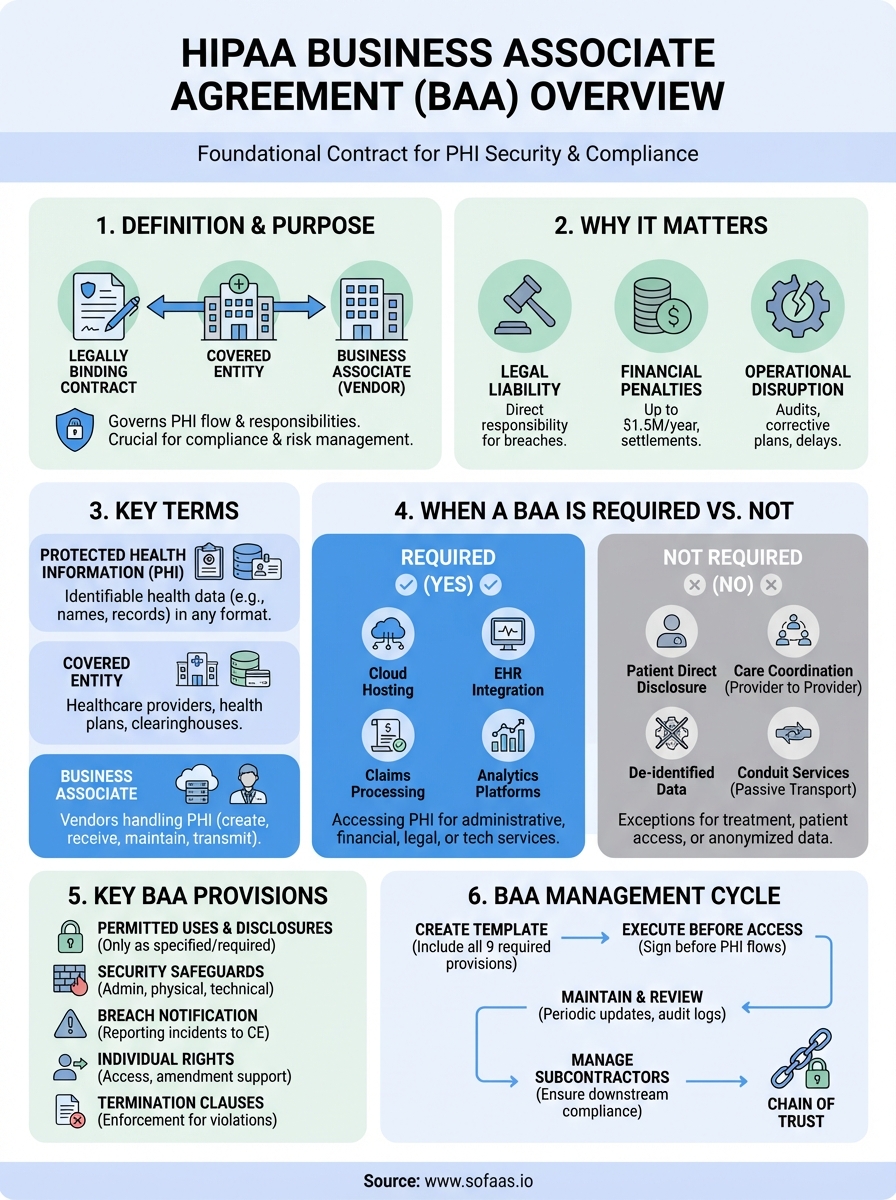
When your healthcare application handles patient data, you're not just building software, you're stepping into a regulated environment with specific legal requirements. At the center of those requirements sits the business associate agreement definition: a legally binding contract that governs how Protected Health Information (PHI) flows between covered entities and the vendors they work with.
If you're integrating with Electronic Health Records or processing patient data through platforms like SoFaaS, understanding BAAs isn't optional, it's foundational to your compliance strategy. These agreements spell out who's responsible for what when PHI changes hands, and they carry real penalties when things go wrong. For healthcare innovators focused on building great applications rather than navigating compliance complexities, knowing the basics of BAA requirements helps you choose the right integration partners from the start.
This guide breaks down what a Business Associate Agreement actually is, who needs one, and what specific provisions HIPAA requires. Whether you're a healthcare supplier connecting to EHR systems for the first time or a technology leader scaling an existing solution, you'll walk away with a clear understanding of your BAA obligations and how to fulfill them.
Why business associate agreements matter for HIPAA
The business associate agreement definition extends far beyond paperwork. HIPAA regulations place direct legal liability on both covered entities and their business associates when PHI is compromised or mishandled. Without a properly executed BAA, your company assumes full responsibility for any breach or violation, regardless of where the actual failure occurred. This liability framework means your integration partners' compliance failures become your compliance failures in the eyes of regulators.
The enforcement landscape and financial consequences
Federal enforcement of HIPAA violations doesn't distinguish between well-meaning mistakes and deliberate misconduct when PHI is exposed. The Office for Civil Rights (OCR) has levied penalties ranging from $100 to $50,000 per violation, with annual maximums reaching $1.5 million per violation category. These aren't theoretical numbers. In 2023 alone, OCR collected over $7 million in settlements from organizations that failed to implement proper business associate safeguards or executed deficient BAAs.

Your organization faces financial exposure from multiple angles: federal penalties, state-level enforcement actions, class-action lawsuits from affected patients, and the operational costs of breach notification and remediation.
Beyond monetary penalties, you face operational disruption when OCR launches an investigation. Corrective action plans often require comprehensive audits of your entire compliance program, mandatory training for all staff, and ongoing monitoring for years. These interventions consume executive time, redirect engineering resources, and delay product development cycles precisely when your healthcare application needs momentum.
How BAAs protect your business operations
A well-structured BAA creates a contractual framework that defines exactly how your vendors must handle PHI, what security measures they must implement, and how they must respond to breaches. This framework lets you verify compliance before data flows rather than discovering gaps after an incident. When you're building healthcare applications that integrate with EHR systems, the BAA becomes your primary tool for managing third-party risk.
Documentation requirements embedded in BAAs also protect you during audits. When OCR reviews your compliance program, they examine whether you've conducted proper due diligence on business associates, whether your agreements contain all required provisions, and whether you've maintained oversight of vendor activities. Your BAAs serve as evidence that you've taken reasonable steps to protect patient information, which directly influences penalty calculations if violations occur.
Strategic implications for healthcare technology companies
For healthcare suppliers and software developers entering the market, BAA requirements shape your entire vendor selection process. You can't simply choose the cheapest integration platform or the fastest EHR connector. Instead, you must evaluate whether potential partners will sign BAAs, whether they maintain HIPAA-compliant infrastructure, and whether they carry adequate insurance coverage. This evaluation process takes time and expertise that many early-stage companies lack.
Competitive positioning also hinges on your BAA readiness. Healthcare organizations won't pilot your application or sign enterprise contracts until you demonstrate mature compliance practices. They need assurance that working with you won't expose them to regulatory risk. Your ability to produce a comprehensive BAA quickly, backed by proper security certifications and compliance documentation, directly impacts your sales cycles and market expansion speed.
Key terms that shape the BAA definition
The business associate agreement definition relies on specific HIPAA terminology that determines whether you need a BAA, what it must contain, and how it applies to your operations. These terms aren't abstract legal concepts. They directly affect which contracts you must sign, what data handling procedures you must implement, and when regulatory obligations attach to your healthcare application. Understanding these foundational terms lets you evaluate your compliance status accurately and communicate requirements clearly with your integration partners.
Protected Health Information (PHI)
PHI encompasses any health information that can identify an individual patient, whether that identification is direct or indirect. This includes obvious identifiers like names, Social Security numbers, and medical record numbers, but it also covers less obvious elements like geographic subdivisions smaller than a state, dates directly related to an individual, and biometric identifiers. When your application processes patient demographics, clinical notes, lab results, or appointment schedules tied to specific people, you're handling PHI that triggers BAA requirements.

Digital health data falls under PHI protection the moment it passes through your systems, regardless of format. This means API responses from EHR integrations, cached patient records, log files containing identifiable health information, and even temporary data structures during processing all count as PHI. Your compliance obligations don't end when data leaves your production database. They extend to backups, disaster recovery systems, and development environments where PHI might reside.
The scope of PHI protection reaches every system and process that touches patient data, creating compliance obligations across your entire technology stack.
Usage and disclosure restrictions
BAAs define exactly how you can use and disclose PHI received from covered entities. Usage refers to internal handling of patient information within your organization, while disclosure covers any sharing of PHI with external parties. Your contract must specify permitted purposes, such as providing services to the covered entity, performing required functions, or complying with legal obligations. Any use or disclosure outside these defined purposes requires explicit authorization from the covered entity or the patient themselves, which creates practical limitations on how you can leverage health data for product development or analytics initiatives.
Who qualifies as a covered entity
The business associate agreement definition hinges on correctly identifying covered entities, because you only need a BAA when you're performing services for an organization that falls into this category. HIPAA defines three specific types of covered entities: healthcare providers who transmit health information electronically, health plans that pay for medical care, and healthcare clearinghouses that process health information. Your compliance obligations kick in the moment you handle PHI on behalf of any organization meeting these criteria, which means you must verify your clients' covered entity status before data integration begins.
Healthcare providers who transmit electronically
Any provider who conducts standard healthcare transactions electronically qualifies as a covered entity, regardless of organization size. This category includes hospitals, physician practices, dentists, chiropractors, nursing homes, and pharmacies. When you build an application that integrates with EHR systems at these facilities, you're working with covered entities. The electronic transmission requirement captures billing processes, claims submissions, benefit verification, and coordination of care activities conducted through digital channels. Even solo practitioners become covered entities when they submit insurance claims electronically or use EHR systems that exchange patient data with other providers.
Your application triggers BAA requirements the moment it touches PHI from any healthcare provider conducting electronic transactions, regardless of whether that provider has two employees or two thousand.
Health plans and insurance organizations
Health plans encompass group health plans, health insurance issuers, HMOs, Medicare, Medicaid, and employer-sponsored plans that provide medical benefits. When your healthcare application processes eligibility checks, claims data, or member information for these organizations, you're handling PHI from covered entities. This category extends to third-party administrators managing benefits on behalf of employer plans, government programs providing healthcare coverage, and specialized plans covering dental, vision, or prescription benefits. Your integration partnerships with health plans automatically establish you as a business associate requiring proper contractual protections.
Healthcare clearinghouses and data processors
Clearinghouses perform data transformation services that convert health information between different formats or standards. These entities take non-standard data from providers and translate it into standardized formats that health plans can process, or they perform the reverse conversion. When your application routes claims, eligibility inquiries, or remittance data through clearinghouse services, you interact with covered entities. Billing services, repricing companies, and community health information systems often function as clearinghouses. Your technology stack may include clearinghouse functionality without you realizing it, particularly when you process FHIR data conversions or handle format standardization for multiple EHR platforms.
Who qualifies as a business associate
The business associate agreement definition centers on identifying which organizations perform functions or activities involving PHI on behalf of covered entities. You qualify as a business associate when you create, receive, maintain, or transmit PHI while providing services to a covered entity. This relationship doesn't require direct patient contact or clinical involvement. Your role in processing, storing, or analyzing health information for covered entities establishes you as a business associate, regardless of whether that work happens through software integration, cloud hosting, consulting services, or administrative support.
Services that trigger business associate status
Your organization becomes a business associate through specific functional relationships with covered entities rather than through formal designations. When you provide claims processing, data analysis, utilization review, quality assurance, billing, benefit management, practice management, or repricing services that involve PHI access, you operate as a business associate. IT vendors fall into this category when they maintain servers storing PHI, provide EHR systems, manage patient portals, or offer cloud infrastructure where health data resides. Legal, accounting, and consulting firms qualify as business associates when their services require PHI review, even if healthcare isn't their primary business focus.
Your business associate status depends on your actual access to PHI during service delivery, not on your company's industry classification or primary business purpose.
Technology platforms and healthcare integrations
Software developers and integration platforms enter business associate relationships the moment they handle PHI transmission between systems. When you build applications that pull patient data from EHR systems, synchronize health records across platforms, or process clinical information for covered entities, you function as a business associate. This includes API integrations, data warehousing services, backup solutions, and analytics platforms that touch identifiable patient information. Cloud service providers hosting PHI-containing databases qualify as business associates, as do companies offering security monitoring, penetration testing, or vulnerability scanning services that access PHI during their work.
Your status as a business associate persists throughout the entire data lifecycle. If you receive PHI for initial processing but maintain copies for disaster recovery, audit trails, or system optimization, you remain a business associate for all PHI retention periods. Subcontractors you engage to help deliver services to covered entities also become business associates, creating a chain of BAA requirements that extends through your vendor relationships.
When a BAA is required and when it is not
The business associate agreement definition provides clear boundaries for when contractual protections become mandatory, but applying these rules to real-world scenarios requires careful analysis of your data access patterns and service relationships. You need a BAA whenever you create, receive, maintain, or transmit PHI on behalf of a covered entity, but several specific exceptions eliminate this requirement even when health information changes hands. Understanding these distinctions prevents both unnecessary contractual delays and dangerous compliance gaps that expose your organization to regulatory penalties.
Situations that require a BAA
Your organization must execute a BAA before accessing PHI when you perform administrative, financial, legal, or operational services for covered entities. This requirement applies when you process claims, conduct quality assessments, analyze utilization patterns, provide legal counsel involving patient records, or offer billing services. Technology integrations trigger BAA requirements the moment your application pulls patient demographics, clinical notes, lab results, or appointment data from EHR systems. Even temporary PHI access during system testing, data migration, or troubleshooting establishes you as a business associate requiring proper contractual protections.
Cloud service providers hosting applications that store PHI need BAAs before covered entities deploy systems on their infrastructure. Subcontractors you engage to help deliver services to covered entities also require BAAs, creating a chain of contractual obligations that extends through your vendor relationships. When you provide analytics platforms that process identifiable patient information, maintain backup systems containing PHI, or offer security monitoring services that access health data, you operate as a business associate regardless of whether healthcare represents your primary business focus.
When you don't need a BAA
Covered entities don't require BAAs when disclosing PHI directly to individual patients or their personal representatives, because patients control their own health information under HIPAA's access rights. Treatment providers exchanging PHI for patient care coordination operate under a specific regulatory exception that eliminates BAA requirements between covered entities. When a covered entity shares de-identified data that meets HIPAA's strict anonymization standards, removing all 18 specified identifiers and ensuring no reasonable basis exists for identification, BAA protections become unnecessary because the information no longer qualifies as PHI.
Your BAA obligations disappear when you work exclusively with properly de-identified datasets that contain no elements capable of identifying individual patients.
Conduit services that merely transmit PHI without accessing content also escape BAA requirements. Internet service providers, postal services, and courier companies transporting sealed records don't need BAAs because they function as passive delivery channels. Your organization similarly avoids BAA requirements when you provide general office supplies, building maintenance, or other services with no PHI access, even when working inside healthcare facilities where patient information exists.
What a HIPAA-compliant BAA must include
The business associate agreement definition specifies nine required provisions that every contract must contain before you can legally handle PHI on behalf of a covered entity. HIPAA regulations outline exact contractual terms that protect patient information, establish liability boundaries, and create enforcement mechanisms when violations occur. Your BAA must address specific use cases, security obligations, and reporting requirements that go far beyond generic confidentiality language. Missing even one required provision puts both your organization and your covered entity client at risk of regulatory penalties, regardless of your actual security practices or good intentions.

Required provisions and obligations
Your BAA must explicitly state that you will only use or disclose PHI for purposes specified in the contract or as required by law. This provision creates clear boundaries around data handling and prevents scope creep that could violate HIPAA regulations. The contract must require you to implement appropriate safeguards that prevent unauthorized PHI use or disclosure, including administrative, physical, and technical security measures aligned with HIPAA's Security Rule. You need contractual language requiring your subcontractors to agree to the same restrictions and conditions that apply to you, creating a chain of responsibility throughout your vendor ecosystem.
BAAs must address individual rights by requiring you to make PHI available for access requests, provide information for accounting of disclosures, and incorporate amendments when covered entities direct you to do so. Your contract needs provisions allowing covered entities to terminate the agreement if you violate material terms, creating enforcement mechanisms beyond regulatory action. These termination clauses give your clients practical tools to protect themselves when your compliance fails, which directly impacts your business continuity and client relationships.
Security and breach notification requirements
Your BAA must require you to report security incidents to covered entities, including both confirmed breaches and suspected unauthorized PHI access. The contract should specify reporting timelines, required information elements, and communication channels for breach notifications. You need provisions requiring documentation and compliance verification, allowing covered entities to audit your practices, review security measures, and confirm that you maintain proper safeguards. These audit rights let clients verify your compliance before problems occur rather than discovering gaps during regulatory investigations.
Your BAA transforms abstract HIPAA requirements into enforceable contractual obligations that create direct liability when security measures fail or reporting requirements go unmet.
The agreement must address PHI return or destruction when your service relationship ends, specifying how you'll dispose of patient information, what retention periods apply for legal or operational purposes, and how you'll certify proper data handling. Your contract should establish that covered entity obligations under HIPAA flow down to you as a business associate, making these regulatory requirements directly enforceable through contract law rather than relying solely on federal enforcement actions.
BAA vs NDA and other confidentiality agreements
The business associate agreement definition establishes specific legal obligations that generic confidentiality agreements simply cannot address. Many healthcare technology companies mistakenly believe that existing NDAs or confidentiality clauses protect them when handling PHI, but these standard agreements lack the regulatory requirements that HIPAA mandates. Your organization needs to understand exactly what separates BAAs from other protective contracts, because using the wrong agreement type creates compliance gaps that federal auditors will identify immediately. Non-disclosure agreements serve valuable purposes in business relationships, but they cannot substitute for BAAs when PHI changes hands between covered entities and their vendors.
Why standard NDAs fall short for HIPAA compliance
NDAs create contractual obligations to keep information confidential but don't address the specific security measures, breach notification requirements, or individual rights provisions that HIPAA demands. Your typical NDA might prevent disclosure to third parties, but it won't require you to implement administrative safeguards, encrypt data at rest and in transit, or maintain audit trails of PHI access. These technical and procedural requirements form the core of HIPAA compliance, and generic confidentiality language simply doesn't cover them.
Standard confidentiality agreements protect business interests but leave both parties exposed to regulatory penalties when PHI requires HIPAA-specific protections.
Breach notification timelines represent another critical gap. NDAs typically require notification of confidentiality breaches "promptly" or "within a reasonable time," but HIPAA establishes specific deadlines of 60 days for patient notification and immediate reporting to covered entities for unauthorized PHI access. Your NDA won't create these precise obligations, which means you could comply with contractual terms while violating federal regulations simultaneously.
Key differences that impact your contracts
BAAs include termination provisions triggered by material breaches that NDAs don't require. When you violate BAA terms, covered entities must either cure the breach or terminate the relationship, creating enforcement mechanisms beyond standard contract remedies. Your BAA must also address subcontractor agreements, requiring downstream vendors to accept the same HIPAA obligations, while NDAs typically don't create this chain of responsibility through your vendor ecosystem.
The scope of protection differs fundamentally between agreement types. NDAs protect proprietary information and trade secrets that parties define, while BAAs specifically govern PHI as HIPAA defines it. You can't narrow BAA protections through contractual language or exclude certain types of health information from coverage, but NDAs let parties negotiate exactly what qualifies as confidential. This regulatory foundation makes BAAs non-negotiable in their core requirements, even when both parties would prefer different terms.
How to create, sign, and maintain BAAs
The business associate agreement definition provides the framework, but implementing these contracts in your healthcare technology operations requires systematic processes that ensure every vendor relationship starts with proper protections. You need workflows for generating compliant agreements, securing signatures before data access begins, and maintaining these contracts throughout their lifecycle. Your BAA management strategy directly impacts how quickly you can onboard new covered entity clients, respond to regulatory changes, and demonstrate compliance during audits. Healthcare suppliers and software developers who treat BAAs as one-time paperwork exercises miss critical opportunities to strengthen vendor relationships and protect their organizations from evolving compliance risks.
Creating a compliant BAA template
Your BAA template must include all nine required provisions that HIPAA mandates while addressing your specific service offerings and data handling practices. Start with language from the Department of Health and Human Services sample agreements, but customize sections to reflect your actual PHI use cases, security measures, and operational procedures. Generic templates downloaded from the internet often contain outdated provisions or miss industry-specific requirements that apply to healthcare technology integrations. Your legal counsel should review any template before you deploy it with clients, ensuring that termination clauses, liability limitations, and indemnification provisions align with your business model and risk tolerance.
Contract language should specify permitted uses of PHI based on services you deliver, whether that's EHR integration, claims processing, or data analytics. Include clear definitions of what constitutes a reportable security incident, establishing thresholds that trigger notification requirements. Your template needs provisions addressing subcontractor agreements, data retention periods, and procedures for returning or destroying PHI when service relationships end.
The signature and execution process
You must execute BAAs before accessing any PHI from covered entities, making signature workflows critical to your sales and onboarding timelines. Establish processes that route agreements to appropriate stakeholders for review, capture electronic signatures that meet legal validity requirements, and maintain signed copies in accessible repositories. Your contract management system should track signature dates, renewal terms, and notification requirements that trigger future actions.
Your BAA becomes legally binding the moment both parties sign, creating immediate obligations for security measures, breach notification, and compliance reporting that you must fulfill starting that day.
Ongoing maintenance and review cycles
BAAs require periodic review to ensure they reflect current regulatory requirements, address new service offerings, and incorporate lessons from security incidents or audit findings. Schedule annual reviews of all active agreements, checking whether permitted uses still match actual data handling practices. When HIPAA regulations change or new guidance emerges from federal agencies, you need processes to assess impact on existing BAAs and execute amendments with covered entity clients. Your maintenance workflow should track agreement expiration dates, renewal requirements, and documentation proving ongoing compliance with contractual obligations throughout the relationship lifecycle.
Managing subcontractors and the BAA chain
The business associate agreement definition extends beyond your direct relationship with covered entities. When you engage third-party vendors to help deliver services, those subcontractors become business associates of business associates, creating a compliance chain that you must manage. Your BAA with covered entities explicitly requires you to ensure that any downstream vendors handling PHI accept the same restrictions and conditions that bind you. This cascading responsibility means you can't simply delegate HIPAA compliance to subcontractors and walk away. You remain liable for their actions, security failures, and breach notification lapses.
Subcontractor BAA requirements and documentation
You must obtain written BAAs from every subcontractor who will create, receive, maintain, or transmit PHI while supporting your services. This requirement applies whether you hire cloud hosting providers, engage consultants for data analysis, or contract with developers for application maintenance. Your subcontractor agreements must contain the same HIPAA provisions that your primary BAA includes, creating identical obligations for security safeguards, breach reporting, and individual rights protections. Without these downstream contracts in place, you violate your agreement with covered entities the moment subcontractor work begins.
Your compliance chain remains only as strong as your weakest subcontractor link, making vendor selection and contract management critical risk management activities.
Documentation requirements extend throughout the entire vendor ecosystem. You need to maintain copies of all executed subcontractor BAAs, track renewal dates, and demonstrate ongoing oversight of their compliance practices. During audits, regulators expect you to produce evidence that you've conducted due diligence on subcontractors before engagement, verified their security capabilities, and monitored their performance throughout the relationship. These documentation obligations create administrative overhead that many healthcare technology companies underestimate when building their vendor networks.
Oversight and monitoring procedures
Your responsibilities don't end when subcontractors sign BAAs. You must implement active monitoring processes that verify ongoing compliance with contractual obligations and HIPAA requirements. This includes conducting periodic security assessments, reviewing audit logs for unauthorized access, and confirming that subcontractors maintain required certifications like SOC 2 Type II or HITRUST. When subcontractors experience security incidents, you need reporting mechanisms that ensure immediate notification so you can fulfill your own breach reporting obligations to covered entities within required timelines.
Vendor performance reviews should include compliance verification as a standard agenda item. Ask subcontractors to provide evidence of security training completion, vulnerability remediation, and incident response capabilities. Your monitoring strategy needs escalation procedures that trigger action when subcontractors fail to meet contractual standards, including contract termination processes that protect covered entity PHI during vendor transitions.
Wrap-up and next step
The business associate agreement definition establishes legal frameworks that protect patient information while enabling healthcare innovation. You now understand which relationships require BAAs, what provisions these contracts must include, and how to manage them throughout their lifecycle. This knowledge lets you evaluate integration partners based on their compliance readiness rather than discovering gaps after you've committed resources to vendor relationships.
Your next step depends on where you are in your healthcare technology journey. If you're building applications that integrate with EHR systems, prioritize partners who handle BAA requirements as part of their service offering. Launch your Smart on FHIR app with platforms that maintain HIPAA-compliant infrastructure and execute BAAs before data flows, eliminating the complexity of managing separate compliance relationships. When you choose integration partners who take full responsibility for security, breach notification, and regulatory obligations, you free your team to focus on building great healthcare applications instead of navigating compliance requirements.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.