Sprinto SOC 2: Process, Pricing, And What To Expect In 2026


Getting SOC 2 certified used to mean months of spreadsheet wrangling, expensive consultants, and a whole lot of guesswork. Sprinto changed that by turning compliance into a more automated, trackable process, and if you've been researching Sprinto SOC 2 specifically, you're probably weighing whether it's the right tool to get your organization audit-ready. The short answer: it's one of the strongest compliance automation platforms available right now, but the details matter.
This article breaks down how Sprinto handles the SOC 2 certification process from end to end, the actual steps involved, what it costs in 2026, how long it takes, and where users say it shines or falls short. Whether you're a startup prepping for your first SOC 2 Type II audit or an established team looking to cut renewal overhead, you'll find practical answers here instead of vendor fluff.
We built SoFaaS with SOC 2 Type II compliance baked into the infrastructure because our customers, healthcare developers integrating with EHRs, can't afford to work with platforms that treat security as an afterthought. That process gave us direct experience navigating SOC 2 requirements, from evidence collection to continuous monitoring. So this isn't a surface-level overview; it's grounded in what we've learned operating a compliant healthcare platform day to day.
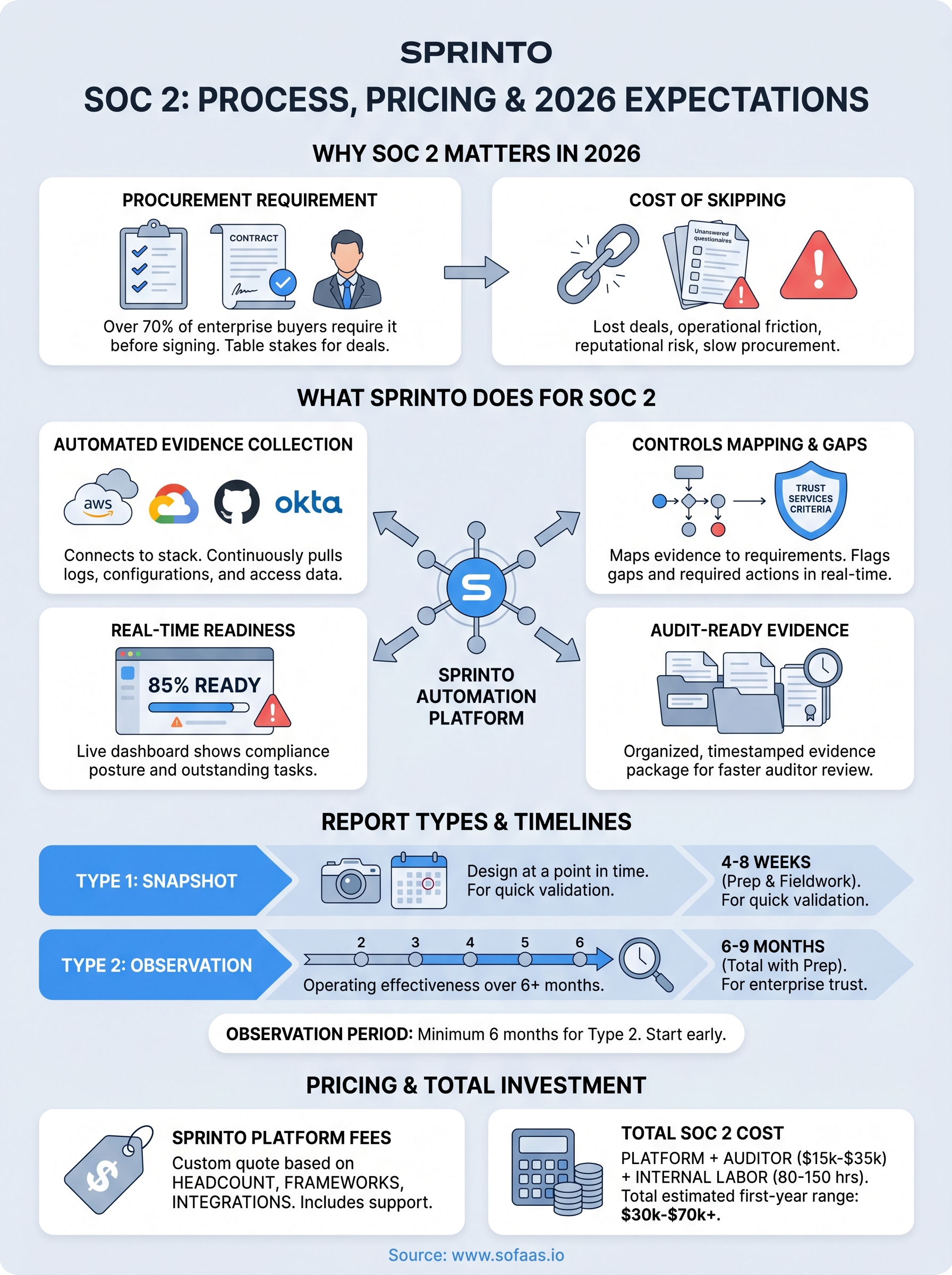
Why SOC 2 still drives buying decisions in 2026
SOC 2 has been around for years, but its role in enterprise sales hasn't faded. If anything, it carries more weight in 2026 than it did five years ago. Buyers, particularly in regulated industries like healthcare, finance, and government contracting, now treat a SOC 2 report as table stakes before they'll even schedule a security review call. If you're selling software or services to any mid-market or enterprise account, the question isn't whether you need SOC 2; it's how fast you can get it done.
SOC 2 has become a procurement requirement, not just a trust signal
The shift happened gradually, but it's firmly in place now. Procurement teams at large organizations routinely include SOC 2 Type II in their vendor checklists, and many will reject a proposal outright if the report is missing or expired. Research from the Cloud Security Alliance shows that over 70% of enterprise buyers require proof of third-party security audits before signing contracts with SaaS vendors.
If you don't have a current SOC 2 report when an enterprise prospect asks for it, you're not just losing a deal point; you're likely losing the deal entirely.
This is why Sprinto SOC 2 automation and tools like it have seen rapid adoption. Companies can no longer treat compliance as a year-end project. Continuous monitoring and always-ready audit evidence are what buyers expect to see when they dig into your security posture.
The cost of skipping SOC 2 goes beyond lost deals
Skipping SOC 2 doesn't just stall enterprise deals; it creates broader business risk and operational friction. Without a report, your security and legal teams spend hundreds of hours answering individual customer questionnaires, each one covering roughly the same ground a SOC 2 report would answer automatically. That overhead compounds fast as your customer base grows.
Your reputational exposure also increases without certification. A data breach or compliance incident at a vendor without a SOC 2 report draws a very different reaction than one at a certified vendor. Certification doesn't make you immune to incidents, but it demonstrates that you built documented security controls with external validation, which matters when you're explaining an incident to a customer's legal and risk team.
Why regulated industries apply extra pressure
Healthcare and finance buyers operate under their own compliance obligations, which means every vendor they work with extends their risk surface. A hospital system procuring a SaaS product doesn't just want to know that your software works; they need evidence that you protect the data flowing through it. SOC 2 Type II provides that evidence in a format that satisfies most procurement and legal review processes without requiring a custom audit each time.
At SoFaaS, we see this dynamic play out directly with our customers who build healthcare applications that handle patient data and EHR integrations. Their enterprise clients scrutinize every layer of the stack, and our SOC 2 Type II certification isn't a marketing badge; it's a document that moves through procurement faster than a stack of self-attested security questionnaires ever could. If you operate in a regulated space, a current SOC 2 report isn't optional; it's the price of entry for the accounts that matter most.
What Sprinto does for SOC 2 teams
Sprinto is a compliance automation platform built to reduce the manual work that slows SOC 2 audits down. It connects to your existing tech stack, pulls evidence automatically, maps that evidence to SOC 2 Trust Services Criteria, and tracks your readiness in real time through a central dashboard. You're not replacing your auditor with Sprinto; you're giving your auditor a cleaner, faster path through the evidence they need to issue your report.

Automated evidence collection across your stack
The most time-consuming part of any SOC 2 audit is gathering proof that your controls are actually working. Sprinto handles this by integrating directly with the services you already use, including AWS, Google Cloud, GitHub, and Okta, and pulling configuration data, access logs, and policy confirmations on an ongoing basis. You don't run a one-time snapshot before the audit window opens; the platform monitors continuously and flags any control drift the moment it appears.
The difference between manual and automated evidence collection isn't just speed. Automated systems don't miss a log or grab the wrong screenshot under deadline pressure.
This continuous monitoring is what separates Sprinto SOC 2 preparation from building a spreadsheet tracker and hoping nothing changes between now and your audit fieldwork. When your auditor arrives, your evidence is current, organized, and tied directly to the criteria it satisfies rather than buried in folders across three different drives.
Controls mapping and gap identification
Sprinto maps your existing configurations to the specific SOC 2 Trust Services Criteria that apply to your selected scope, whether you're pursuing security, availability, confidentiality, or multiple categories. You see at a glance which controls pass, which have evidence gaps, and which require new policies or processes before you're audit-ready.
This mapping helps you avoid overbuilding your control set, which is one of the most common mistakes teams make on their first SOC 2. Sprinto shows you exactly what each criterion requires and what your current environment already covers, so you spend effort only where it actually counts toward the audit outcome.
For teams doing their first SOC 2, this structured approach is one of the most practical parts of the platform. You're not starting from a blank checklist; you're starting from a pre-mapped framework that reflects both the standard requirements and your specific technical environment from day one.
SOC 2 Type 1 vs Type 2 and when to do each
Before you configure anything in Sprinto, you need to decide which report type you're pursuing, because Type 1 and Type 2 have fundamentally different scopes and serve different purposes. Picking the wrong one wastes time and money, and your auditor will tell you the same thing if you ask.
What Type 1 actually tells an auditor
A SOC 2 Type 1 report captures a snapshot of your controls at a single point in time. Your auditor reviews whether your security controls are designed appropriately to meet the Trust Services Criteria you selected, but they don't evaluate whether those controls performed consistently over weeks or months. You get a report that says, in effect, "on this date, these controls existed and were reasonably designed."
Type 1 reports are faster to obtain, typically requiring four to eight weeks of preparation, and they cost less to produce. That makes them useful in specific situations: you're under a hard deadline from a prospect, you've recently built out your security program and want external validation quickly, or you want to identify gaps before committing to a longer Type 2 observation period. Type 1 is a starting point, not a destination.
What Type 2 adds and why it carries more weight
A SOC 2 Type 2 report covers an observation period, usually a minimum of six months, during which your auditor verifies that your controls operated effectively and consistently throughout that window. This is the report that enterprise procurement teams want to see, because it demonstrates sustained control performance rather than a one-day snapshot.
Most enterprise buyers won't accept a Type 1 in place of a Type 2 for contracts involving sensitive data. If your target market includes healthcare or finance, Type 2 is the report you need to close those deals.
When you run a Sprinto SOC 2 program, the platform supports both report types, but its continuous monitoring and automated evidence collection are specifically built for Type 2 workflows. The observation period doesn't catch you off guard because Sprinto collects evidence on an ongoing basis rather than in a pre-audit scramble.
Choosing the right starting point for your situation
Your decision should come down to two factors: timeline pressure and buyer requirements. If a specific enterprise deal requires a report within 60 days and no Type 2 exists yet, start with Type 1 and begin your Type 2 observation period immediately after. If you have six months before your first major enterprise review, skip Type 1 entirely and invest that time in building a clean Type 2 observation window from the start.
What you must set up before you use Sprinto
Sprinto does a lot of the heavy lifting once it's running, but the platform can only work with what you give it. If you start onboarding without clarity on your scope, your system inventory, and your team structure, you'll spend the first few weeks undoing decisions instead of making progress. A few hours of upfront preparation pays back in weeks of smoother audit execution, and skipping this groundwork is the single most common reason Sprinto implementations start slowly.
Define your scope before you touch the platform
Your SOC 2 scope determines which systems, services, and data flows fall inside the boundary your auditor will evaluate. Sprinto maps controls and collects evidence based on what you declare in scope, so defining this incorrectly creates gaps that surface at the worst possible moment. Work with your engineering and product leads to identify every system that stores, processes, or transmits customer data, and document that boundary in writing before your first Sprinto session.
The scope decision also drives which Trust Services Criteria you select. Security is mandatory, but availability, confidentiality, and processing integrity each add control requirements that change how you configure the platform. Most first-time teams start with Security only and expand in a later renewal cycle, which keeps the initial audit focused and manageable.
Get your integrations and access ready
Sprinto pulls evidence automatically from your cloud infrastructure, identity providers, code repositories, and endpoint management tools. Before you connect anything, confirm you have admin-level credentials for each integration target, including AWS, GCP, or Azure, Okta or your identity provider, GitHub or your version control system, and your MDM solution. Collecting these access credentials in advance eliminates the most common onboarding delay teams run into.
Waiting until after onboarding to track down admin credentials can push your observation period start date back by two to four weeks, which matters a lot when you're working against a deal deadline.
Assign clear ownership across your team
Sprinto SOC 2 workflows assign controls to specific people who are responsible for maintaining them and responding to failures. If you haven't decided who owns security controls, HR-related policies, or vendor management before you start, those assignments sit unacknowledged and stall your readiness score. Identify a compliance lead and at least one technical owner per major control category before your kickoff call with Sprinto's onboarding team.
How the SOC 2 process works with Sprinto
Once your scope is defined and your integrations are connected, Sprinto SOC 2 follows a clear, stage-based workflow that moves you from initial setup through audit completion. The platform doesn't hand you a blank checklist and wish you luck. Instead, it builds a live readiness dashboard that shows your current compliance posture, what's failing, what needs attention, and what's already satisfying a control requirement based on your existing configuration.
Getting connected and setting your baseline
After onboarding, Sprinto scans your connected infrastructure and generates an initial control readiness score based on what it finds. Each integration contributes data points that map directly to Trust Services Criteria, so you see immediately which controls are passing, which are failing, and which require human action like uploading a policy document or completing a team training task. This baseline assessment typically surfaces 10 to 20 gaps for most early-stage companies, and having them visible on day one gives your team a concrete work list rather than vague compliance anxiety.
Your readiness score isn't just a progress bar; it reflects the actual evidence state your auditor will evaluate, which means improving it translates directly into a faster audit.
Completing controls and preparing for your auditor
From your baseline, the work splits into two tracks running in parallel. The first track is automated: Sprinto monitors your integrations continuously and updates control status as your environment changes. The second track is manual: your team completes policy approvals, runs required security training, reviews vendor risk assessments, and handles other human-dependent tasks that no automation tool can do for you. Sprinto surfaces these tasks in a prioritized queue so your compliance lead knows exactly where to spend time each week.
When you're ready to begin the audit, Sprinto generates a structured evidence package organized by criteria and control. Your auditor receives clean, timestamped proof for each item rather than a folder of mismatched screenshots and spreadsheets. Most Sprinto customers report that audit fieldwork moves significantly faster compared to manual preparation because the auditor spends less time requesting missing items and more time actually reviewing evidence. Once fieldwork closes, your auditor issues the report, and Sprinto immediately begins tracking your next observation period so your renewal cycle starts without losing momentum.
What evidence Sprinto can collect and what it cannot
Understanding where automation ends and human work begins is critical before you commit to any compliance platform. Sprinto handles a substantial portion of evidence collection without any manual effort on your end, but it operates within specific technical boundaries. Knowing those boundaries upfront helps you staff your compliance program correctly and avoid surprises when your auditor requests evidence that Sprinto can't generate on its own.
What Sprinto pulls automatically
Sprinto SOC 2 automation covers the evidence categories that live inside your connected integrations. Once you link your cloud provider, identity management system, endpoint management tool, and code repository, Sprinto continuously collects configuration states, access control lists, encryption settings, audit logs, and change management records from those systems. It captures user access reviews, multi-factor authentication enforcement status, and backup configuration data without requiring anyone to run a manual check or export a report.
The strongest argument for automated evidence collection isn't just speed; it's accuracy, because Sprinto timestamps every data point it collects, giving your auditor a verifiable chain of evidence rather than a screenshot taken the day before fieldwork.
For availability and incident management controls, Sprinto also pulls uptime data and alert configurations from integrated monitoring tools, which satisfies a significant portion of what auditors look for when evaluating your operational reliability.
What still requires manual input
Several control categories sit outside what any automation platform can handle, and Sprinto is transparent about this. Vendor risk assessments require your team to review third-party security documentation and make a judgment call, not pull a config file. Security awareness training completion records need to be uploaded or tracked through a connected HR system, and the actual training content has to be created or sourced separately.
Policy documents, including your information security policy, access control policy, and incident response plan, require human drafting and approval workflows before Sprinto can mark those controls as satisfied. Sprinto provides templates and tracks acknowledgment status across your team, but the content and sign-off process belong to you. Physical security controls also fall outside the platform's reach entirely; if your scope includes an on-premise environment, you'll need to document physical access controls manually and provide that evidence directly to your auditor. Mapping these gaps early keeps your compliance timeline realistic.
Sprinto pricing and what affects your total SOC 2 cost
Sprinto doesn't publish a flat price on its website, which frustrates a lot of teams early in the evaluation process. Pricing is custom-quoted based on your company size, the number of integrations you need, and which compliance frameworks you're pursuing. For SOC 2 specifically, most startups with 10 to 50 employees report annual platform fees in the range of $12,000 to $20,000, while larger teams with more complex environments typically land between $20,000 and $40,000 per year. These are platform costs only and don't include your auditor.

What Sprinto charges for its platform
Sprinto structures its pricing around two main factors: employee count and the number of frameworks you activate. If you're pursuing SOC 2 as a standalone framework, your quote will be lower than a team adding ISO 27001 or HIPAA at the same time. You can negotiate multi-framework discounts during initial contract discussions, and most Sprinto sales conversations include an onboarding package covering dedicated customer success support through your first audit. Ask specifically what onboarding support is included before you sign, because the level of hands-on guidance varies by tier.
Key variables that affect your Sprinto quote:
- Company headcount
- Number of compliance frameworks activated
- Number of integrations in scope
- Contracted onboarding support level
The other costs that add up
Your total SOC 2 investment extends well beyond the Sprinto subscription. The auditor fee is the most significant additional cost, and for a SOC 2 Type II with a standard six-month observation period, qualified auditing firms typically charge between $15,000 and $35,000 depending on audit scope, firm size, and how much fieldwork your environment requires. Sprinto can introduce you to audit partners through its partner network, which sometimes results in bundled pricing, but you're free to bring your own auditor.
Your total Sprinto SOC 2 cost for a first-year Type II program, including platform fees and auditor costs, generally falls between $30,000 and $70,000 for most early-stage companies.
Internal labor is the cost most teams underestimate. Even with automation handling evidence collection, your compliance lead and technical owners will spend real hours on policy documentation, vendor reviews, security training, and auditor communication. For a lean startup team, budget for 80 to 150 hours of internal time spread across the preparation and fieldwork phases. That number drops significantly in renewal years once your control infrastructure is already built.
Timelines: what a realistic SOC 2 schedule looks like
Most teams underestimate how long SOC 2 actually takes, not because the work is mysterious, but because they fail to account for onboarding time, policy drafting, and the mandatory observation period that Type 2 requires. When you use Sprinto SOC 2 to automate evidence collection, you cut preparation overhead significantly, but you can't compress the calendar below certain minimums without reducing the credibility of your report.

Type 1 timeline: four to eight weeks
A SOC 2 Type 1 report is the faster path, and with Sprinto connected and your integrations in place, most teams can complete preparation and hand off a clean evidence package to their auditor within four to six weeks. The variables that stretch that window are mostly human: slow policy approvals, missing admin credentials for integrations, and team members who haven't completed security training on schedule.
If you're working against a hard deadline from a prospect, Type 1 is achievable in four weeks for a well-prepared team, but your observation window for Type 2 should start the same day your Type 1 fieldwork ends.
Auditor availability is also a real scheduling constraint. Quality auditing firms book weeks out, so factor in two to four weeks of auditor lead time before fieldwork even begins. Starting your auditor search before your evidence package is ready saves you from sitting on completed prep work while you wait for a slot.
Type 2 timeline: six to nine months from kickoff
A SOC 2 Type 2 program requires a minimum six-month observation period, and that clock doesn't start until your controls are operating correctly. If you need three weeks to fix control gaps identified during onboarding, your observation period shifts accordingly. From first login in Sprinto to receiving a signed Type 2 report, most teams land somewhere between seven and nine months total for their first certification.
The breakdown typically looks like this:
| Phase | Estimated Duration |
|---|---|
| Sprinto onboarding and integration setup | 1 to 2 weeks |
| Gap remediation and policy completion | 3 to 5 weeks |
| Observation period | 6 months minimum |
| Auditor fieldwork and report issuance | 4 to 6 weeks |
What affects your schedule
Two factors compress or extend this timeline more than anything else: how clean your existing security posture is when you start, and how quickly your team responds to open tasks in Sprinto. Companies that enter with documented policies and consistent access controls often shave four to six weeks off the remediation phase. Teams that treat compliance tasks as lower priority than product work consistently push their audit date back by similar margins.
Common SOC 2 pitfalls and how to avoid them in Sprinto
Most SOC 2 failures don't come from a lack of security controls. They come from predictable process mistakes that teams make before and during their audit cycle. Using Sprinto SOC 2 removes many of the manual risks, but the platform can't protect you from strategic errors made before you set it up.
Scoping too broadly on your first audit
Teams frequently try to include every system, service, and data flow in their first SOC 2 scope, which multiplies the number of controls you need to satisfy and extends your preparation timeline without proportionally increasing the value of your report. Your auditor isn't evaluating how large your scope is; they're evaluating how well your controls work within whatever boundary you define.
A focused, well-controlled small scope produces a stronger first report than an ambitious wide scope with gaps scattered throughout.
Start with the minimum scope that covers your core product and customer data. In Sprinto, your scope definition drives which integrations you need to connect and which control categories appear on your readiness dashboard, so getting this right before onboarding saves you from reconfiguring halfway through the observation period.
Letting manual tasks pile up while automation runs
One of the most common mistakes Sprinto users make is treating automated evidence collection as a signal that compliance work is mostly done. Automation handles your infrastructure evidence, but your policy approvals, vendor risk reviews, and security training completions stay on a manual queue. Teams that deprioritize those tasks discover at the start of auditor fieldwork that dozens of human-dependent controls are still open.
Set a weekly check-in rhythm where your compliance lead reviews open Sprinto tasks and assigns deadlines to anything without a completion date. Treat that queue with the same urgency as your product sprint board, because unresolved manual tasks are the leading cause of delayed audit fieldwork among companies that otherwise have strong automated evidence coverage.
Underestimating auditor availability
Many teams finish their observation period and evidence package only to discover that their preferred auditing firm can't start fieldwork for another six weeks. Quality SOC 2 auditors are consistently booked out, and this scheduling reality doesn't change because your timeline is tight.
Contact at least two auditing firms at the start of your observation period, not the end, and confirm tentative fieldwork dates in writing. Locking that calendar slot early keeps your entire program timeline on track without last-minute scrambles.
Sprinto vs Vanta, Drata, and Secureframe
All four platforms automate SOC 2 compliance evidence collection, and all four will get you to an audit. The differences come down to onboarding speed, pricing structure, auditor relationships, and how much hand-holding your team needs along the way. Before you commit to any platform, you need a clear picture of where each one pulls ahead and where it falls short for your specific situation.
Where Sprinto differs from Vanta
Vanta is the most widely recognized name in compliance automation, and it has a large integration library that appeals to teams already running complex infrastructure. Sprinto tends to edge ahead on customer support quality during the first audit cycle, with more hands-on onboarding guidance included in standard tiers. Vanta's pricing structure also scales faster as your headcount grows, which makes it more expensive for growing teams even when your compliance scope stays constant. If your team is early-stage and wants active guidance through the SOC 2 Type II process rather than a self-serve dashboard, Sprinto is typically the better fit.
Both platforms produce credible audit outcomes, but the difference in support quality during your first observation period can meaningfully affect how smoothly your fieldwork goes.
How Drata compares
Drata competes closely with Sprinto SOC 2 workflows and targets a similar audience of startups and mid-size technology companies. Its interface is polished, and many users find its policy management templates slightly more developed out of the box. Where Drata lags is in pricing transparency during initial sales conversations, and users frequently report longer onboarding timelines compared to Sprinto. Teams that prioritize a fast start over interface design tend to prefer Sprinto's quicker path from first login to active monitoring.
Secureframe and the right fit question
Secureframe positions itself as the budget-friendly option, and its entry-level pricing makes it attractive for pre-revenue startups that need a report but have minimal compliance budget. The tradeoff is a smaller integration library and fewer automated checks for complex cloud environments. If your infrastructure involves multi-cloud setups or a large number of third-party services in scope, Secureframe's coverage gaps will require more manual evidence work to compensate. Sprinto and Drata handle that complexity more reliably, which matters when your auditor starts pulling threads during fieldwork.
Where to go from here
You now have a complete picture of what Sprinto SOC 2 delivers, what it costs, how long it takes, and where the real work falls on your team. The next step is straightforward: define your scope, start your auditor search early, and treat your Sprinto task queue with the same discipline you bring to your product roadmap. The companies that finish fastest are the ones that make compliance work a weekly habit rather than a quarterly sprint.
If you're building a healthcare application that needs to connect with EHRs, compliance doesn't stop at SOC 2. Your customers expect HIPAA-compliant infrastructure and secure data handling at every layer of your stack. SoFaaS handles that integration layer for you, with SOC 2 Type II and HIPAA compliance already built in, so you can focus on your product instead of your infrastructure. See how SoFaaS connects your app to EHRs in days.
The Future of Patient Logistics
Exploring the future of all things related to patient logistics, technology and how AI is going to re-shape the way we deliver care.